Playlist
Cybersecurity Leadership Summit 2018 Europe
Videos from the Cybersecurity Leadership Summit 2018 in Berlin, Germany
Show more
39 videos in this playlist
Event Recording
Cybersecurity Innovation Night 2018 - Machine Learning & Deep Learning for Secure Future
Dec 20, 2018
Every year the number of cyber attacks is increasing. The types of targets include just about everyone, ranging from Fortune 500 companies, small and medium-sized businesses, critical infrastructure, and government agencies.
Cyber-attacks are becoming more sophisticated as well as growing in frequency. Up to a million new malware variants are created every day. Each new threat group can be significantly different from previous ones and can be used in damaging attacks around the world.
The Cybersecurity Innovation Night will focus on cutting-edge approaches and advanced solutions in...

Event Recording
Martin Kuppinger - User Behaviour: The Link between CyberSecurity and Identity Management
Dec 18, 2018
An increasing number of attacks, both external cyber-attacks and internal attacks, are well-thought-out and long-running. Particularly external, targeted attacks rely on the use of zero-day-exploits, which factually are yet unknown exploits. Thus, standard approaches such as signature-based analysis don’t help – you can’t detect what you don’t know. On the other hand, malicious behavior of internal users is hard to detect. Commonly, existing entitlements are used, but not as they should be used. Both challenges can be addressed by analyzing the user behavior and...

Event Recording
Dr. Torsten George - How Zero Trust is Creating a Game-Changing Security Experience
Dec 18, 2018
We got security wrong. Enterprise security is failing with two-thirds of organizations experiencing an average of five or more security breaches in the past two years, according to Forrester. Adding to the fervor is the impact of Cloud, Mobile, DevSecOps, Access. The entire experience of developing, deploying and protecting applications has forever changed. In today’s network perimeter-free world, organizations must adopt a Zero Trust Security model – and shift from ‘trust but verify; to assume users inside a network are no more trustworthy than those outside. And with...

Event Recording
Dr. Frank Dudek - Accelerating Cybersecurity – Is Your Information Security Program Up to Speed?
Dec 18, 2018
Internet content providers rely on fast, modern webapps and feature-rich web frameworks to drive customers to their sites. In a landscape of accelerating change and continuous code deployment, my keynote will discuss how a company’s cybersecurity program must evolve to remain effective in such fast-paced environments.

Event Recording
Tim Hobbs - DevOps & Service Layers
Dec 18, 2018
IAM products are highly configurable systems tailored to the diverse needs of customer environments and applications. Modern applications require short development cycles and IAM systems that can be adjusted at the same pace. Modern data centers are configuration-driven, resilient environments designed to meet rapidly changing application needs, and modern IAM solutions must be in line with this paradigm.
Introducing traditional IAM products into cloud containers is not a simple "lift and shift" operation, as it once was with the virtual machine infrastructure. Today's...

Event Recording
Dr. Michael von der Horst - The Current Threat Landscape: A 360° View and Effective Remediation Strategies
Dec 18, 2018
In today’s cloud-connected world, the way we work has changed. But security has not. When over half of the PCs in most organisations are mobile, you need to protect your workforce wherever they access the internet – not just when they are in the office. You need to identify attacks as they are staged on the internet, so you can block them before they launch.
Join us as Dr. Michael von der Horst, Senior Director for Cybersecurity Germany at Cisco, takes us through what we see out there “in the wild”. He will present effective defence and remediation strategies...
Event Recording
Paul Simmonds - From Network Protection to Data Security
Dec 18, 2018
"Zero Trust" is the latest security buzzword from the vendors marketing department; but what it actually means for you means should vary depending on your business requirements.
Properly aligning security architecture to enable the business strategy of the organisation is the key to deliver a Zero Trust architecture. But the solution could be anything from implementing identity-aware firewalls to the extremes of "BeyondCorp"; Google's firewall-less global network when the security posture is identical whether you are in Starbucks or on the Google campus.

Event Recording
Klaus Hild - Predictive Governance – Leveraging the Power of Identity Analytics
Dec 18, 2018
In this presentation, SailPoint will explain why Identity Analytics will change the way companies will think about CyberSecurity, by adapting ‘Predictive Governance’.
Predictive Governance will enable organizations to be more effective and efficient at governing access without increasing the risk.
Event Recording
Dragan Pendic - Path to Zero Trust Security - Data Veracity, When Truth Is Essential and Trust Optional
Dec 18, 2018
Businesses are more data-driven than ever, but inaccurate and manipulated information threatens to compromise the insights that companies rely on to plan, operate, and grow. Unverified digital resource is a new type of vulnerability - one that is
chronically overlooked by digital enterprises. With autonomous, data-driven decision making, the potential harm from unverified digital resources become an enterprise-level existential threat. And then, there's a wider cybersecurity aspect and how to address the following:
- Data provenance verification - the history of data from its...
Event Recording
Martin Kuppinger - User Behavior Analytics: Can We? Should We? Must We? And if, How to Do It Right?
Dec 18, 2018
User Behavior Analytics (UBA) or UEBA (User & Entity Behavior Analytics) is an important capability of a variety of products: Specialized solutions for UBA; IAM tools with built-in UBA capabilities; and various cyber-security products that also come with built-in UBA capabilities.
The question to start with is: What is UBA really and how does it differ from e.g. Threat Analytics, SIEM, Access Governance, and other capabilities? Where is the benefit of UBA? Is it a nice-to-have or must-have in these days of ever-increasing cyber-threats? And if we go for UBA: How do we do it right?...

Event Recording
Yaniv Avidan - AI Powered Data Herding in Hybrid Cloud Environments
Dec 18, 2018
Having cloud software tools and services entering our core business processes, it becomes even more critical that we govern information across platforms, the diverse forms of data and at scale. Artificial Intelligence plays a significant role in enabling companies keep their business running faster, more protected in hybrid cloud environments, while optimizing the Hardware and Software stack.

Event Recording
Gal Helemski - How a Policy Based Approach Dramatically Improved Access Control and Authorization
Dec 18, 2018
Hear how a leading multinational Financial institution was able to evolve from Role Based Access Control (RBAC) to the new paradigm, Policy Based Access Control (PBAC), and learn what challenges this solved, and the ROI they were able to see from using PBAC.

Event Recording
Peter Gyongyosi - Can You Trust UBA? -- Evaluating Machine Learning Algorithms in Practice
Dec 18, 2018
The promise of every security solution is to detect the next attack, but verifying that claim is almost impossible. Attacks are extremely rare and tend to change: the ability to catch attacks that happened in the past say little about the ability to find things that will happen in the future and those breached are unlikely to share information and data about how that happened. In this presentation I will show the different approaches and metrics we found to measure the efficiency of the unsupervised machine learning algorithms commonly used in UBA products.

Event Recording
Alexei Balaganski - The Sorry State of Consumer IoT Security and How Can We Possibly Fix it
Dec 18, 2018
The Internet of Things has already become an integral part of our daily lives, whether we like it or not. In the office, at home, and even in the street, we are surrounded by a multitude of smart devices ranging from smart TVs and fridges to network routers, voice assistants and parking meters. No matter how different their functionality is, however, all these “things” share two major common traits: they are all connected to the public Internet and they lack the most basic security controls.
For decades, security was never a priority for embedded device manufacturers. Modern...
Event Recording
Alexei Balaganski - Containers, Microservices, APIs: The Latest DevOps Security Trends
Dec 18, 2018
To stay competitive during the times of digital transformation, when business models and technology landscapes change daily, enterprises must reinvent many of their business processes to achieve new levels of agility and flexibility, and nowhere else this is more evident than in software development. As the demand for faster design, development and delivery of software is growing, organizations are adopting the DevOps methodology that fundamentally changes the ways software is produced.
With a strong focus on practices like continuous delivery, infrastructure as code and test...
Event Recording
Richard Bell - Developing a Strategy for Managing Incidents
Dec 18, 2018
For many years now, the management of incidents has been a challenging, dynamic and somewhat accidental in response. Today, whatever the threat we face, there is zero margin for errors if affected and excuses are certainly a thing of the past. Planning for the worst-case scenario is now commonplace, yet is it tested? and who is involved? Developing the right strategy for your organisation and its operations is key to continued success and minimising the impact of any incident. This presentation intends to encourage the consideration of different approaches, thinking, and conversations...

Event Recording
Chris Burtenshaw - User Behaviour Analytics (UBA) - The Enterprise Value Proposition
Dec 18, 2018
This session explores what UBA is and the value it brings to enterprise security in context of other common controls and tools. Chris will give some history of how user activity monitoring has changed, and its challenges, and the state today. Finally, we will discuss how this is changing and what to look out for as organisations are consuming more cloud-based services.
Event Recording
Dimitri Chichlo - What is the Role of a CISO in 2020?
Dec 18, 2018
In the past years, a CISO would mainly be chosen among the IT staff who expressed his interest for information security or by arbitrarily promoting someone from the inside to please the auditors with filling a headcount gap. Tasks and skills were mainly technical, focusing on patching, administering firewalls and installing antiviruses. With the years though, companies have made their IT systems the backbone of their businesses. Similarly, criminality has shifted to exploit online systems. Combination of both realities now requires that CISOs possess and demonstrate core competencies that...
Event Recording
Peter Dornheim - Build Up a Security Operation Center and Provide Added-Value to Business Operations
Dec 18, 2018
Make or buy? Budget annihilator or business driver? Only 2 questions which must be answered when building up a Security Operation Center. How to address these questions and how to start a project to establish a Security Operation Center in a traditional German manufacturing company is content of this session.
- Start small, think big: Understand how to start a SOC project and deliver an added-value fast - Think big: Identify a SOC target vision which maps to your individual company situation - Be prepared: Learn about typical challenges during the SOC ramp-up...

Event Recording
Mans Hakansson - Beyond OAuth: Securing APIs with Policies & Attribute-Based Access Control
Dec 18, 2018
Attribute Based Access Control (ABAC), OAuth 2.0 and OpenID Connect (OIDC) are complementary standards that can be used individually or in concert to offer comprehensive access control for applications that are built using microservice and API approaches. -API security basics -Avoiding bad security practices -Overcoming OAuth limitations -Managing authorization as a microservice
Event Recording
Tom Hofmann - Effective Countermeasures For Securing Critical Infrastructure – A View On The Human Aspect
Dec 18, 2018
When we think of security in the OT / IoT space, we are very focused on technological measures and controls. However, the recent incidents in this field showed that security events are not only based on a failure of technical controls. The 2017 Triton malware attack on SaudiAramco is a good example of what can happen based on human behaviour. While the attacked Triconex SIS controller is protected by a physical switch, it seems that this switch has been left in program mode. The ongoing digitalization of operational technologies presents cyber security professionals a whole new challenge....
Event Recording
H. Huetter, B. Peeters and D. Roeper - Managing Complexity in a CIAM Migration Project - A Case Study of the ‘Steinberg ID’ Project
Dec 18, 2018
To handle the digital identities of customers efficiently is key to deliver valuable digital services. This entails a change of the core infrastructure, leading to a critical operation for many stakeholders and raising challenges in different domains. These challenges not only affect technical architecture and implementation, but also processes, communication and even organizational structures. In this talk, we will give an overview of how Steinbergapproached those challenges. This includes topics like: - How to handle the huge complexity of such a project, technically and...
Event Recording
Panel - Risk Assessment and Security Design
Dec 18, 2018
Zero Trust Security assumes that nothing in a companies ITinfrastructure like including users, endpoint devices, networks, and resources, is ever trusted. All interactions must be verified to decrease the chance of a security breach. Zero Trust Security ensures secure access to resources while significantly reducing the possibility of access by bad actors. In this paneldiscussion we will discuss the considerations companies should make before implementing Zero Trust Security and Zero Trust Security by Design.

Event Recording
Panel - AI and the Future of Cybersecurity
Dec 18, 2018
Advanced analytical technologies will help organizations in their fight against cyber-attacks. These technologies assist in detecting potential attacks at an earlier stage, as well as enabling the identification of complex attack patterns that span various systems. In this panel we will discuss the role of AI in the future of cybersecurity, possibilities of using it as a weapon by adversaries and the possibility of developing preventing techniques using Machine Learning and Deep Learning.
Event Recording
Dr. Rachel Suissa - Mapping the Comprehensive Cyber Human Factor with Implications on AI and Future Cyber Leadership
Dec 18, 2018
The aim of this presentation is to map the comprehensive human factor and cybercrime landscape categories (Motivations, the category of the perpetrator, category of the targets and victims, opportunistic and targeted attacks, the jurisdiction of the target, technology versus social engineering). Mapping these two pillars provides indicators that can be integrated in AI cybercrime predictive analysis, construct a model of the man-cognitive system and a cyber leadership network based on the deduction of cyber policy challenges.

Event Recording
Panel - Future of Critical Infrastructure Security
Dec 18, 2018
More often we hear about the devastating effects the attack on critical infrastructure can have on the citizens of an affected city or a country. Yet we don't see large scale attacks yet being conducted. Panellist will discuss possible threats in todays world as well as the ways private sector and governments can collaborate to prevent such assaults on critical infrastructure.
Event Recording
Panel - Achieving Consistent Enterprise Security
Dec 18, 2018
In this discussion the panellists will speak about the types of attacks which enterprises should expect in coming years. The ways of DevOps integration into an enterprise security program will also be discussed together with best practice highlights.
Event Recording
Dragan Pendic - Application Security - Achieving Security at Speed and Scale
Dec 18, 2018
Modern software development for cloud-native world requires continuous application security to go along with continuous integration, continuous delivery, and continuous deployment. Sadly, even well-established application security programmes often can’t operate at the speed and scale required. We will look into the ways of rethinking legacy security infrastructure and processes and how to adapt in the complex world of digital business and advanced attacks.
Event Recording
John Tolbert - Defense-in-Depth: New Kinds of Tools for All the Layers
Dec 18, 2018
The principle of defense-in-depth remains a key design element for enterprise organizations. Although many have said that perimeters are going away, or identity is the new perimeter, the fact is that almost all enterprises still have perimeters. The names may have changed, and components may be declared “next-gen”, but there are still firewalls, VPNs, intrusion detection and prevention systems, etc. We will look at how new kinds of tools have become available to help protect against attacks from the application to the network layers.
Event Recording
Matthias Reinwarth - CIAM as a Building Block of an Online-Success Story
Dec 18, 2018
Consumer Identity and Access Management (CIAM) encompasses many aspects. On the one hand, it is about optimizing the usability of services through technologies and practices to make it easier and secure for users sign up for a service. For the service providers, CIAM is all about lifecycle management of identities of many kinds - ensuring that accounts are set up, changed, and deactivated (or deleted) in a timely, accurate and secure manner. And for even more people, it focuses on security and compliance through technologies and practices that facilitate auditing and governance activities,...
Event Recording
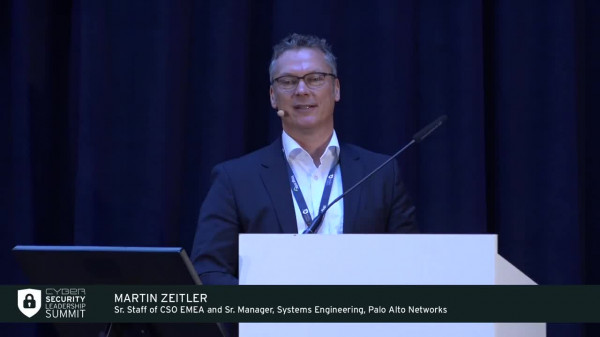
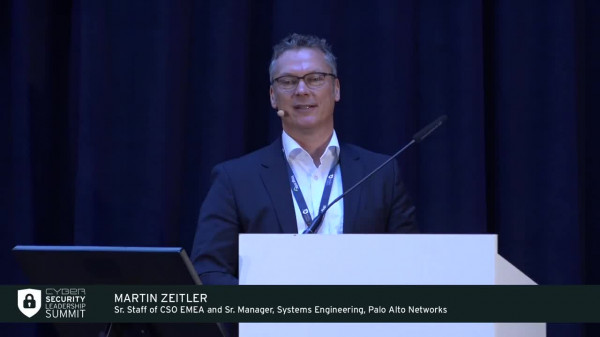
Martin Zeitler - Your Move to “the Cloud” Secured
Dec 18, 2018
There is a tremendous amount of business value that you can get from “the cloud”. But, there are a lot of challenges in adopting these services securely. The real question is how we can approach “the cloud” from a security perspective in order to really get that full benefit of the offerings.

Event Recording
Marko Vogel - Cyber Security as Part of Industry 4.0
Dec 18, 2018
- More aggressive, complex and well organized: Cyber threat landscape on the rise
- Cyber Security – added value for industry 4.0?
- Industry 4.0 needs company-specific security strategies
Event Recording
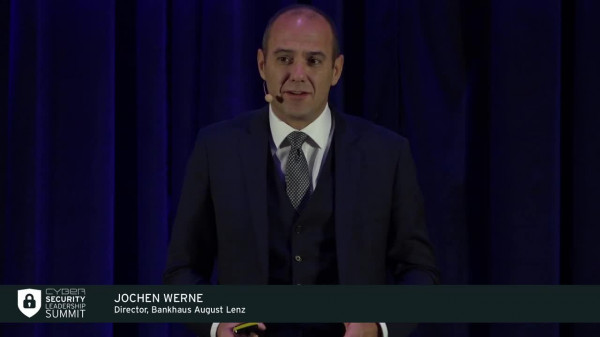
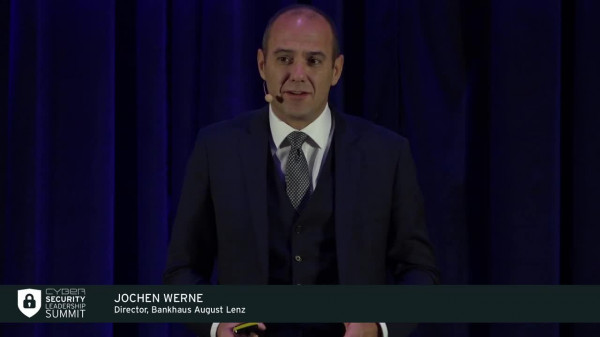
Jochen Werne - The Future of Digital Business Security
Dec 18, 2018
The digital development spurts have captured all areas of life. Industry 4.0 is on everyone's lips. The digitization of all areas of work and life requires integrated and robust strategies and processes at all levels. Consequently, this poses many questions: How well prepared are economies and politics as well as the society as a whole with regard to cyber safety aspects? How do people react to change processes? Basically, what is the significance of the human factor in the overall context of digital safety and cybersecurity? Of course, there have been prior leaps in developments within...
Event Recording
Maximilian Möhring - Die Zukunft Digitaler ID ist Dezentral – Aber Nicht Blockchain
Dec 04, 2018
Die Identitätslandschaft ist voll von IAM-Systemen, Identifikations- und Authentifizierungsanbietern, verschiedenen Technologiestandards und wird durch nationale sowie branchenspezifische Normen geregelt.
Die Lösung für dieses Problem ist die Interoperabilität der Lösungen indem der Markt vereint wird und die Integration bestehender Identitätsanbieter vereinfacht wird. Obwohl Blockchain neue ID-Lösungen liefern kann, löst sie nicht die Kernproblematik des Identitätsmarktes. Revolution wird durch die Evolution des bestehenden Marktes...
Event Recording
Martin Lum - Dezentralisierte Blockchain Identität BYODID ohne Zwischenhändler
Dec 04, 2018
Viele der neuen DID und Self-Sovereign Identitäts-Konzepten verlangen weitreichende neue Strukturen und Verfahren. Ihr Schwerpunkt ist der Austausch maschinell lesbarer Identitäts-Unterlagen zwischen Behörden und vertrauenden Geschäftspartnern. Anstatt Zwischenhändler abzuschaffen, so wie von den Blockchain Propheten versprochen, werden neue Führungsnetzwerke aufgebaut um technische Neuigkeiten traditionell zu verwalten.

Event Recording
Dr. Andre Kudra - Dezentrale Digitale IDs und die Vorzüge der Blockchain Technologie
Dec 04, 2018
Um den Dschungel von Authentifizierungsverfahren und digitalen Identitäten zu bändigen, werden oftmals Single Sign-on (SSO) Strukturen geschaffen. Dadurch wird es Nutzern ermöglicht viele Logins mit nur einer digitalen Identität zu verwalten und Authentifizierungsverfahren je nach Bedarf einer Applikation anzupassen. SSO-Applikationen haben jedoch einen entscheidenden Nachteil: Sie setzen ein Vertrauen in nur eine Instanz, z. B. den Entwickler der Applikationen, oder mehrere Instanzen voraus. Was wäre, wenn wir für jeden Onlinedienst oder...

Event Recording
Workshop - Mobile Apps und Single Sign-On
Dec 04, 2018
Wenn es um die Integration von Mobile Apps in die Single Sign-On-Umgebung geht, dann entstehen oft Interessenskonflikte zwischen Designern, der IT-Sicherheit und dem, was der Kunde wirklich möchte.
Welchen Einfluss hat das gewählte Login-Verfahren auf die Sicherheit und welche Ansätze haben sich in der Praxis bewährt? Wie kann ein Kompromiss aussehen, der sowohl den Kunden zufriedenstellt, aber trotzdem ein ausreichendes Sicherheitsniveau bietet? Erfahren Sie, welche Best Practices es gibt und welche Rolle OAuth 2.0 dabei spielt.

Event Recording
Andre Priebe - CIAM & API Management
Dec 04, 2018
Customer Identity & Access Management und API Management sind als Business Enabler bekannt. Aber in Kombination sind sie sogar mehr als die Summe ihrer Teile.
Erfahren Sie, wie digitale Identitäten Ihrer Kunden und Ihrer APIs das digitale Ökosystem Ihrer Kunden infiltrieren, um sie noch stärker an Ihr Unternehmen zu binden. Verstehen Sie, warum die Weitergabe von Kontrolle an Dritte und externe Entwickler der Schlüssel zum Erfolg dieses Ansatzes ist und dass die Einhaltung von Standards Voraussetzung dafür ist.

Event Recording
Cybersecurity Leadership Summit 2018 Europe Summary
Nov 14, 2018