Modern and hybrid operating models, Software-as-a-Service, regulatory requirements, working from home, various types of internal and external users, and the phenomenon of BYOD (bring your own device) are challenges we have to face today. Such challenges are constantly emerging, which demands a flexible approach. Often these flexible requirements result in many specific sub-solutions for particular problems. This causes the company to have no central overview of which services, which devices, and which applications are used and for what purpose.
To challenge the internal IT teams even further, we have a professional cyber-crime industry. These people try to steal data or to blackmail organizations, based on existing gaps in systems, applications, processes, and protection mechanisms.
Connect and manage everything – Security must not have gaps
The goal of every company must be to contain and structure this uncontrolled growth. An open architecture that meets future requirements must be at the forefront of enterprise security efforts. KuppingerCole has developed the Security Fabric for this purpose. It is based on the experience gained from consultancy work at numerous international companies.
KuppingerCole’s Security Fabric – Connect Everything
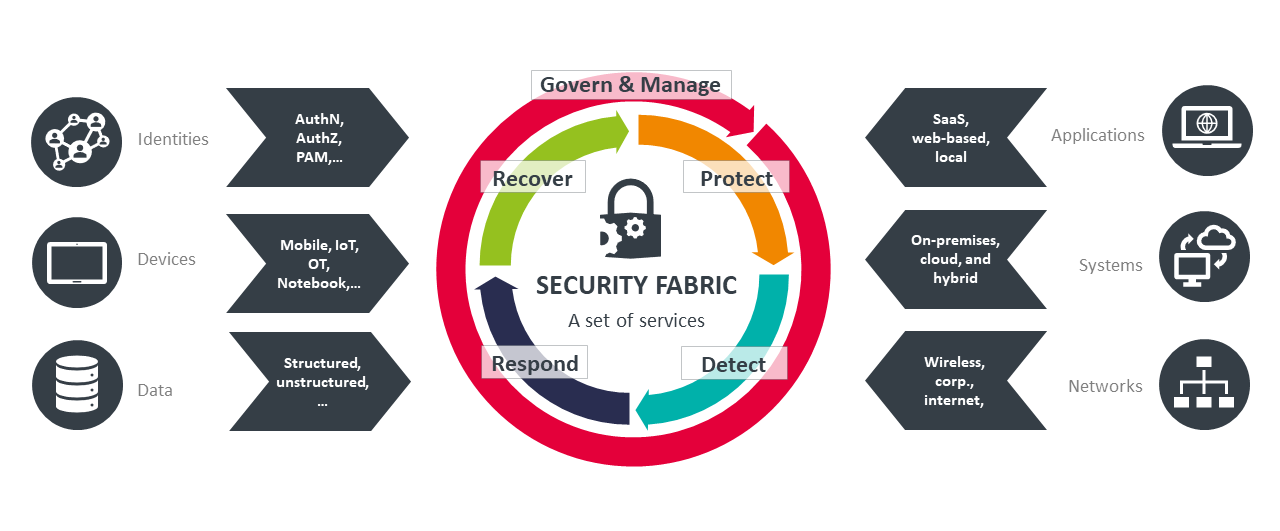
The KuppingerCole Security Fabric connects all types of identities to access devices, data, applications, systems, and networks. The goal is to achieve consistent security from end to end for everything. The most important point is that no access is unmanaged or ungoverned. At the center of the Security Fabric are five core topics that a well-defined Security Architecture must include:
- Govern and Manage – Security Frameworks, Risk Assessment and Asset Classification and general IT Risk Management are the core components here. Governance and Security Management must be ensured.
- Protect – Spans from Data Security to Enterprise Information Protection to Network Security and Malware Protection. The purpose of these Building Blocks is to protect Data, Applications, Systems, Networks and End Points.
- Detect – The objective is to detect potential attacks by using various monitoring and Security Intelligence mechanisms. Usually, this is implemented by a Security Operation Center or Cyber Defense Center.
- Respond – Determining what to do in response to a cyber-attack is an essential part of a comprehensive Cybersecurity approach. Incident Response Planning and Processes are fundamental pre-defined processes to ensure all stakeholders know what to do in response to an incident.
- Recover – It is mandatory to develop the ability to recover from an incident and to have some flexibility enabled by Operational Resilience. Business Continuity Management helps organizations to keep some of their core services running – even when they are actively under attack.
Using a fabric concept helps to organize and structure capabilities and services
The Security Fabric is not a concrete product or service. It is a toolset and paradigm to define the right building blocks, to bundle them within capabilities, and to define services such as a “Protection and Detection Service” or a “Respond Service”. These services are the foundation of the organization’s IT Security. Applications must integrate into the Security Fabric to benefit from advanced, central, and modern security concepts. This method also helps security organizations to have a central approach and overview.
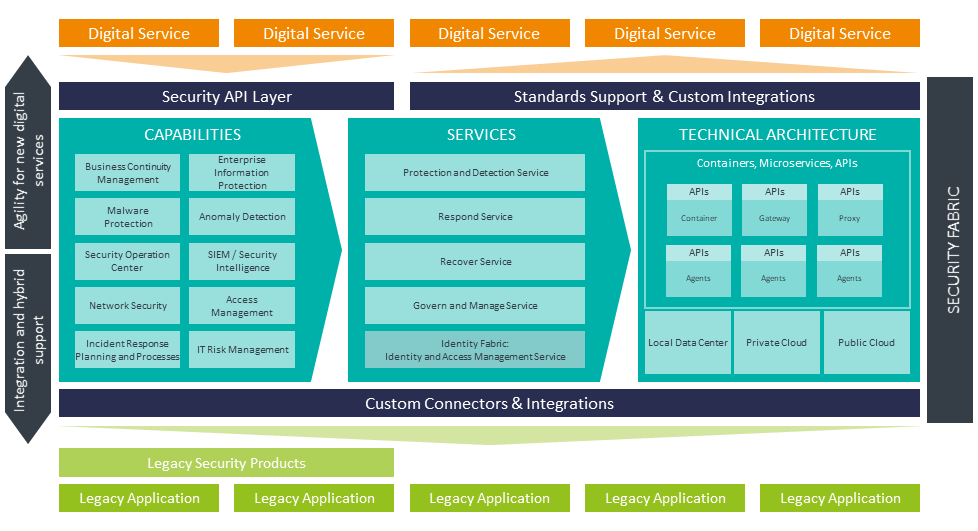
KuppingerCole’s Security Fabric – A set of services
A key benefit of the Security Fabric is to maintain an overview of the zoo of applications and services that run within an organization. The fabric helps to structure the existing services, show the gaps and reveal the existence of duplicated services. This helps to improve the general portfolio, to optimize technology investments, and to improve security on a continual basis.
Security Fabrics improve cybersecurity and flexibility
Some things to look for when choosing your Security Fabric:
- An open, integrated and extendable architecture is the standard for the Security Fabric to meet today's requirements and be open for those of tomorrow. It should support different deployment models with identical capabilities, whether on-premises or as a service.
- With dynamic orchestration and intelligence capabilities at the core, it should provide you with the flexibility and agility you need to build new digital services or integrate with legacy systems.
- Pay attention to building up a reliable toolset that can be fully integrated and easily extended by new services to fulfill future requirements.
Having a Security Fabric in place helps organizations improve their portfolio, their spending, and their cybersecurity because this takes a business-centric view of the things you really need. KuppingerCole provides specialized support to help organizations to improve their security as well as their security architecture by using the Security Fabric.


















































