If you start considering the topic of cybersecurity in your company, you’ll quickly realize that there are many facets. In traditional companies, IT has grown in parallel to meet the requirements in digitization and production in a timely manner.
These traditional companies and their suppliers with physical products such as automobiles often have a somewhat higher degree of maturity in general Enterprise Risk Management, which only deals in part with IT-relevant risks.
Companies that were founded more recently, or that offer their products or services on a purely digital level have a slightly different character. Companies that have a high level of digital services usually have a higher demand for IT risk management. The risk management in such companies has typically a higher maturity level for IT risks rather than in Enterprise Risk Management. It is contrary whether you are good at IT risk management or Enterprise Risk Management. It depends on your history and your core business. Many companies do not have the same maturity level in both.
For instance, the start-up that has achieved strong growth within a few years will have taken steps to ensure that the digital services are secured, but a mitigation measure for a water pipe burst in the office may not exist.
Enterprise Risk Management is much more than managing single risks from Business Operations and IT
An important basis for risk management in a company is to be aware of the various types of risks that a company must consider and that risks from different categories may be related. Enterprise Risk Management differentiates between 4 categories of risk.
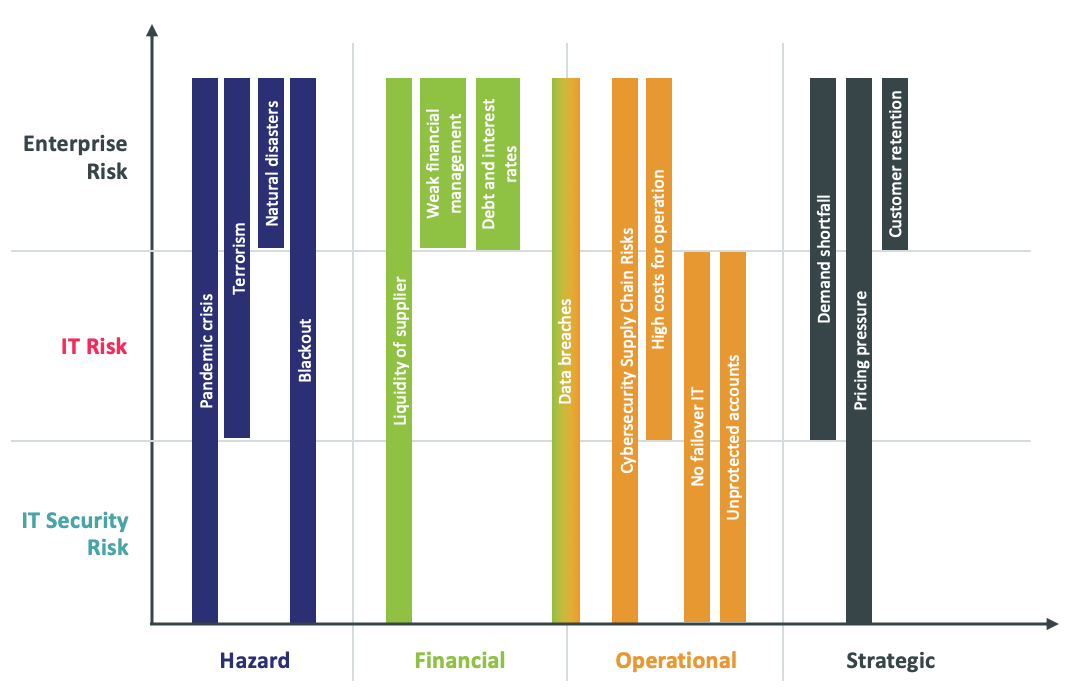
- Hazards coming from outside, such as earthquakes or quarantine, and damage to other people's property.
- Risks that can have an impact on the financial situation of a company. Typical examples are liquidity shortages or falling prices on the market. Risks related to customer satisfaction and the product.
- Especially if the company is offering digital services, those IT risks are handled in this operational category.
- Risks relating to competitors and the strategic orientation or objectives of the organization. The IT relevant incidents can belong to any of these categories depending on the role of the IT whether it is supporting or essential for running a specific area.
Enterprise Risk Management is an integrated process
A company must consequently be aware of its risks in order to be able to implement measures against a risk to mitigate its effects. This is the core of Enterprise Risk Management, which is concerned with assessing and managing all business risks, not only the IT ones. For this process to work, a number of things need to be taken into account and a holistic process needs to be followed.
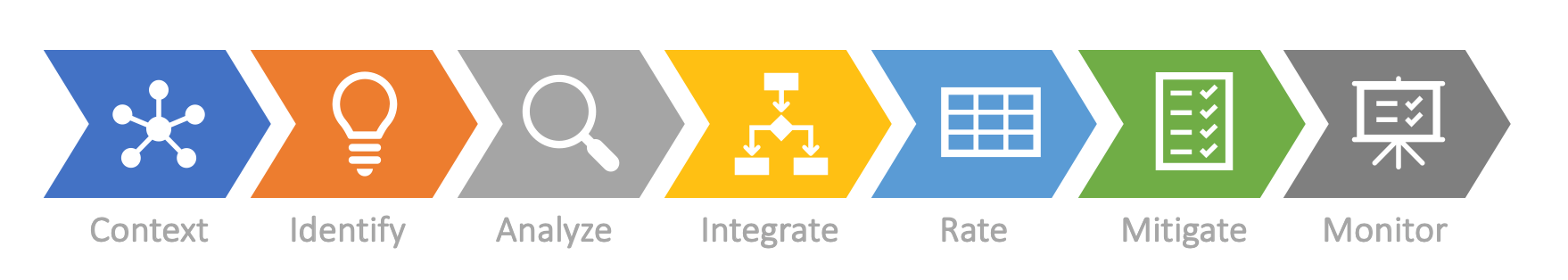
- Context: First of all, you need to understand the organization and the conditions in which the company works to specify the focus of risks. Take for instance the IT-driven startup, with its unique context and challenges.
- Identify: You need to collect the various risks within the different areas of your company. This can be done with the support ISO31000 and ISO 31010 which provide an overview of enterprise risk. Security Frameworks and standards like ISO 27001 or NIST, which can act as a blueprint for general IT-related risks.
- Analyze: Analyzing of the impact to your organization at a detailed level is the next step so that your company can be aware of what could happen if the risks ever materialize.
- Integrate: A critical point is to consider the cascades of risks. A single risk might be harmless but when combined with another harmless one the consequences can be magnified to threaten the very existence of the organization. For instance, having problems with the supplier’s management platform at the same time as having supply failure with your default supplier, can lockdown your production.
- Rate: As well as each risk, the aggregation of risks needs to be rated and prioritized.
The enterprise risk register as an essential component of ERM
Up until this point you just invested time to identify, analyze, and rate risks for your organization. It is very important to have a list and a clear understanding of what could happen to you. This makes the enterprise risk register an essential component of enterprise risk management.
- The next step then is to define the risk level you will accept and the controls that will be needed to ensure this level together with who is responsible. This is really where you can make big improvements to your level of (Cyber) security. You need to be aware of the various layers of Enterprise Risk Management. Don’t forget that the aggregations of risks must also be handled.
- It is also important to understand that your organization changes over time as do the risks. New risks appear while others disappear or become more or less critical. Therefore, you must frequently review the measurements of the risks as well as to work continuously to identify new risks.
Three steps to improve your Cybersecurity with Enterprise Risk Management
- Integrate your IT Risk Management into your Enterprise Risk Management. You need to combine and aggregate risks to check the dependencies and relationships. Especially IT risks and non-IT risks must be considered. It will help you to identify and monitor risks which you might not have had in your focus.
- Use specific tools for brainstorming, collecting, rating, and defining of measures for risks – a risk management tool for enterprise risks. This helps you to organize the risks and maintain the lifecycle of each risk regarding the impact.
- Do not reinvent everything. Risks are specific but for IT and enterprise risks, various blueprints and standards exist which you can use as a base for a deeper level of specification, controls, and mitigating measures. Typical fundaments are COSO and CoBIT. This leads to fast results with manageable effort.
Share your experience with others – participate in our Virtual Event
Having an integrated Enterprise Risk Management strategy in place helps organizations to improve both security and cybersecurity because this takes a business-centric view of potential risks. KuppingerCole provides specialized support to help organizations to improve their security portfolio as well as their security architecture.
If you would like to share your experiences and learn about new topics and trends in enterprise risk management and cybersecurity, join us at the “Cybersecurity & Enterprise Risk Management” Virtual Event, on June 2nd. Participation is free!