In my research for this blog post, I wondered where the proverb about glass houses and throwing stones originated. I'm unsure whether there will ever be a definitive answer, but this one appealed to my education as an English major:
The proverb appeared in Chaucer’s Troilus and Criseyde, written in 1385. Later, George Herbert modified it this way: “Whose house is of glass, must not throw stones at another.” And in 1736, Benjamin Franklin wrote, “Don’t throw stones at your neighbors, if your own windows are glass.”
Then I decided I’d give DALL-E a go at it. I like that it turned out so dramatically:

This image captures quite well the point I’d like to make about breach revelations—piling on the schadenfreude provides little solace when you become the target. And let’s face it, we are all targets now.
For whom the bell tolls
When the closing bell rang at the NASDAQ on November 29, 2023, Okta shares (NASDAQ:OKTA) had been devalued by nearly 7% and received six downgrades from previous estimates, despite the company’s better-than-expected earnings report. According to a TD Cowen analyst report, OKTA's financial performance is reflecting “the impact of recent high-profile breaches involving the company’s solutions.”
In reaction, part practical, part penance, Okta stated it would halt product releases for 90 days (presumably, the time it takes to get one’s security glasshouse in order). Such news may seem like a holiday gift to Okta’s competitors.
But, continuing to draw on my English major, John Donne had this great poem a while back about a bell tolling and then Hemingway went on to develop the concept into a novel. This sentiment rings true today, as we step collectively into an era of hyper-exposure to cyber-attacks: everybody’s going to take their turn. From Donne’s poem:
Any man's death diminishes me,
Because I am involved in mankind.
And therefore never send to know for whom the bell tolls;
It tolls for thee.
Speaking of humanity, it turns out the initial account that was compromised was a non-human—or service—account. These types of accounts can be unruly, and they don’t use multi-factor authentication. In a discussion on infosec.exhange (with Adam Shostack and friends, no less!) commentors offer various summaries on what had just occurred and who was to shame. This one, I think, summarizes it up best:
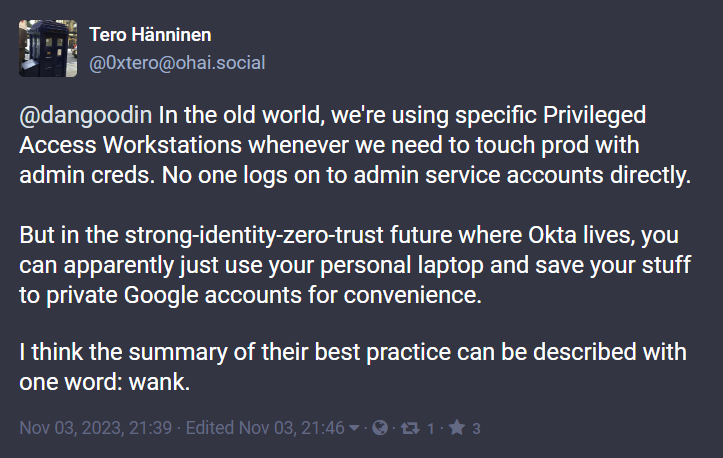 Yes, let’s all agree, the one-word technical summary is accurate. But—to paraphrase a security professional I discussed the matter with—as large as the providers are these days, you can never be certain you’ll have your bases covered everyone takes a turn, even open-source providers.
Yes, let’s all agree, the one-word technical summary is accurate. But—to paraphrase a security professional I discussed the matter with—as large as the providers are these days, you can never be certain you’ll have your bases covered everyone takes a turn, even open-source providers.
And—talk about the mother of all identity providers—the DNA research company 23andMe reported a breach in October, as well—and likewise continues to realize new depths of the severity of the attack. And again, lest we forget, this cautionary tale is at least as old as 2011, when KuppingerCole Analysts reported similar findings from the RSA SecurID breach.
Cyberculture and the culture of silence
So, what is the proper response to getting our security bell rung (as the NFL calls it)? Well, first and foremost, it’s important to talk about it openly. That’s not an easy topic for discussion with investors, customers, and competitors looking on.

BeyondTrust, which reported the breach on October 2nd 2023, was likely the first customer to speak up about it, because the attackers had finally showed up at the company’s door (front door in this case). Still, Okta took more than two weeks to admit to the breach. Oddly, even now, BeyondTrust’s detailed timeline of the breach provides a lot more specifics than you can find on Okta’s security blog.
There’s a reason the mantra of physical security states, “if you see something, say something”—the social alert draws in a community to restore safety. For example, BeyondTrust reveals that the attacker requested a HAR file archive (HTML backup) for the ostensible purpose of troubleshooting the website. Obtaining the file, the hacker then reused a session cookie from that HAR file to attempt a replay attack on a web service, which BeyondTrust easily blocked. Undeterred, the attacker then switched to using API calls instead. According to BeyondTrust:
API actions cannot be protected by policies in the same way as actual admin console access. Using the API, they [the attackers] created a backdoor user account using a naming convention like existing service accounts.
This is great intel on how the threat actor conducts business and everyone should be put on notice. Still, valuable time was spent in a moment or two of silence. Why?
The culture of silence needs to go. We need to swap notes. Safety is a collaborative effort, because we can’t know in advance where the next threat will originate or where it will propagate.
Going to production requires oversight
The interesting thing about this breach is that it started with a service account and then moved to human accounts. One way this happens is by not hardening the system sufficiently when moving from development to production environments. The Okta Developer portal makes it easy for developers to get moving on projects but will need a thorough security review when deploying applications.
Also, the LDAP interface is typically enabled by default even when not in use, heightening the risk level. Access control policies for sensitive apps and admin accounts are often not adequately designed to limit risk exposure to breaches.
Okta is now critical infrastructure and needs a run book that ensures security is maintained. One of the shocking findings in the Cybersecurity & Infrastructure Security Agency (CISA) report on Lapsus$ breaches “organizations did not always consider third parties and BPOs in their risk management programs.” Communication with third parties is necessary preparation for moving to production, as well.
How to learn from—rather that gloat over—others’ mishaps
Proposals for avoiding and dealing with breaches were plentiful at our recent Cyberevolution conference. For example, we heard from Michiel Stoop of Philips, who spoke on “How to Minimize the Blast Radius of an Attack?” In this case, the approach was to minimize access from privileged accounts.
Jorge Monteiro of Ethiack pointed out that it’s actually a good idea to attack yourself first, in his presentation titled “Autonomous Ethical Hacking for Accurate and Continuous Security Testing.”
Emergency preparedness is often overlooked in cybersecurity, with the majority of the attention going to prevention and detection. But, if we already agree that we are all simply waiting our turn to be attacked, it seems only obvious that we prepare plans for that inevitable moment.
One proposal we covered at Cyberevolution is the practice of developing and training on tabletop exercises, which was covered in a panel titled, “Arresting Disaster: Driving Incident Response in Cyber-Regulated Europe in an Age of AI Threats,” which included participants from ArmorText and the law firm of Crowell & Moring. It’s important to recognize that even your messaging platforms like Teams, Slack, or Zoom become compromised in a breach and so your team will need an out of band “break glass” communication that also meets legal requirements of various governments.
Independent of the measures taken to reduce risk and mitigate cyber disasters, the common thread through all these measures is to communicate openly and quickly with the cyber security community. We’ll all fare much better against attackers as we open channels for honest, detailed, and actionable information.
















































