1 Introduction / Executive Summary
This Leadership Compass on Data Security Platforms is already the fourth update to our previous coverage of database security solutions that started over 5 years ago. Previous editions of this rating were released under the title “Database and Big Data Security”, but we believe that the updated title better reflects the current market trends and recognizes changes in messaging of many vendors.
We still recognize database security as a broad section of information security that concerns itself with protecting databases (or more generally, any location where structured digital data is stored) against compromises of their integrity, confidentiality, and availability. This functional area covers various security controls for the information itself stored and processed in database systems, underlying computing and network infrastructures, as well as applications accessing the data.
However, as computing and storage technologies continue to improve, and modern applications embrace distributed, heterogeneous, cloud-native architectures, the very notion of a database is changing as well. The concept of Big Data has already almost completely disappeared – from the modern business perspective, it is all just “data”, regardless of the underlying storage technology.
Following this trend, we have chosen to update the title of this Leadership Compass to align it better with both customer expectations and the strategic vision of vendors in this market segment. We do feel however that the full convergence between traditionally separate security solutions for structured and unstructured data is yet to be observed, and thus we continue to focus primarily on securing structured data stores in this Leadership Compass.
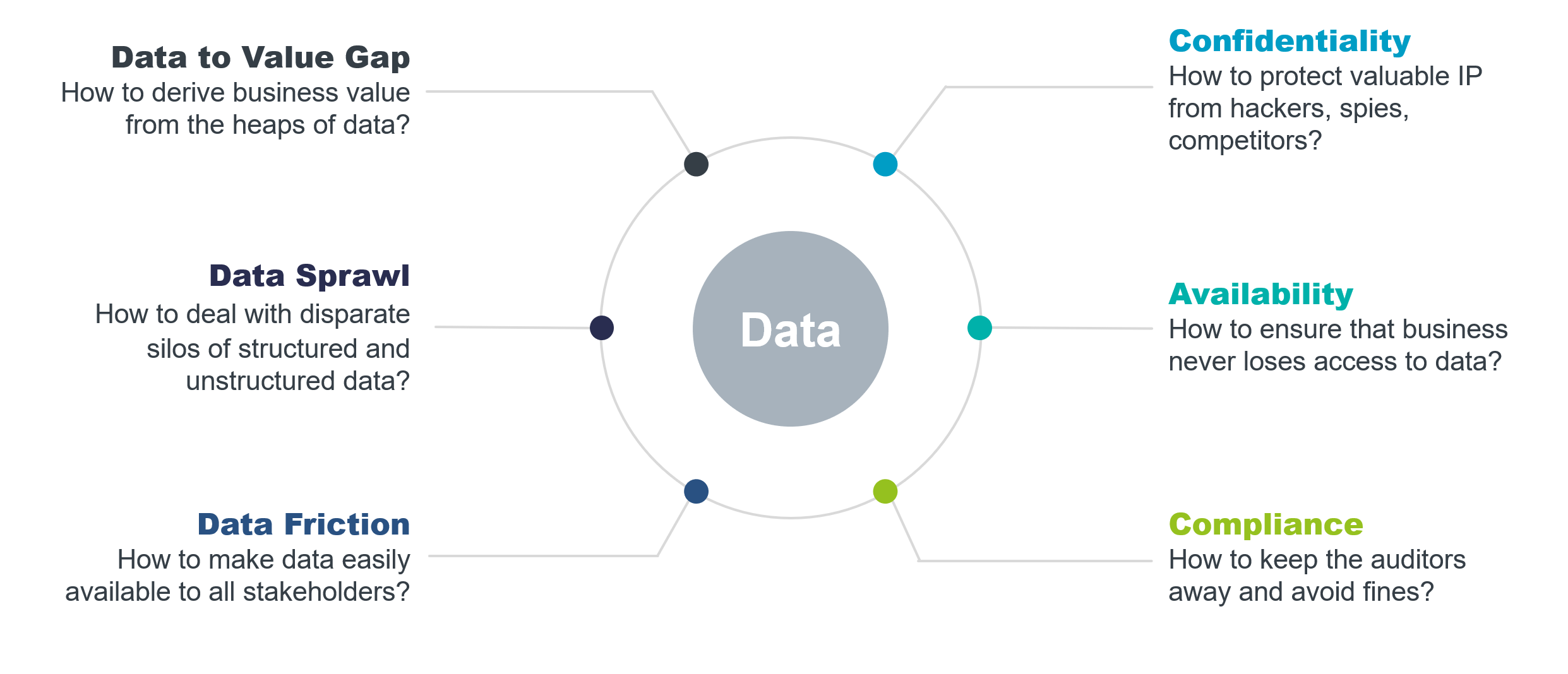
Figure 1: Data challenges the businesses are facing nowadays.
As more and more companies are embracing digital transformation, the challenges of securely storing, processing, and exchanging digital data continue to multiply. With the average cost of a data breach exceeding $4.35M globally (and over $9M in the United States, according to Statista), just direct financial losses can be catastrophic for many companies, not even considering indirect reputational damages. High-profile “mega-breaches” that expose millions of sensitive data records can easily drive these costs up to hundreds of millions of dollars, but even the victims of smaller ones are now facing increasingly harsh compliance fines.
One of the revelations that businesses, that have recently suffered a costly data breach, finally come to is that not all data is the new oil or their “crown jewels”. In fact, some of the data they have collected turned out to be a dangerous liability that can cause massive problems when not handled properly. Often it simply looks like much of the data companies hold has no intrinsic value, since this value is only generated when data is moving or transforming, creating insights, analytics, statistics, etc. – that is, it serves a tangible purpose for a certain business process. A data security platform must be able to sustain these processes, not introduce additional roadblocks.
One can say that, just like an ideal database, an ideal data security solution is one that does its job and does not get in the way. Businesses are begrudgingly dealing with compliance and privacy issues because of the regulations, but data security is very difficult to sell as a business enabler. Most customers do not really want a data security platform; they just want their data to be safe everywhere, at all times, and for any kind of data. They even want this for data in use, even if not all of them really understand the vast complexity of such a solution.
Nowadays, most companies end up using various types of data stores for structured and unstructured information, depending on their business requirements. Data protection regulations like the European Union’s GDPR, California’s CPRA or numerous other country- or state-level laws make no distinction between relational databases, data lakes, or file stores – all data is equally sensitive regardless of the underlying technology stack. Just keeping track of all the digital information is a big problem, but understanding which data is more sensitive according to various policies and regulations and then selecting and enforcing the necessary data protection and governance capabilities is already too much even for the largest businesses.
The area of data security covers various security controls for the information itself stored and processed in database systems, underlying computing and network infrastructures, as well as applications accessing the data. These include, among others, data protection capabilities, fine-grained access controls, activity monitoring, audit, and compliance features as well as other means needed for comprehensive multi-layered protection against external and internal threats. As the amount and variety of digital information managed by organizations continues to grow, the complexity of the IT infrastructure needed to support this digital transformation grows as well.
Among the security risks databases of any kind are potentially exposed to are the following:
- Denial of service attacks leading to disruption of legitimate access to data.
- Data corruption or loss through human errors, programming mistakes, or sabotage.
- Inappropriate access to sensitive data by administrators or other accounts with excessive privileges.
- Malware, phishing, and other types of cyberattacks that compromise legitimate user accounts.
- Unpatched security vulnerabilities or configuration problems in the database software, which may lead to data loss or availability issues.
- Attacks specifically crafted to target databases through application interfaces or APIs, like SQL injections for relational databases and similar exploits for NoSQL and Big Data solutions.
- Sensitive data exposure due to poor data lifecycle management. This includes improperly protected backups, testing or analytical data without proper masking, etc.
- Unsanctioned access to encrypted sensitive data due to improper key management – this is especially critical for cloud environments, where encryption is often managed by the cloud service provider.
- Insufficient monitoring and auditing – not only these pose a significant noncompliance risk, but a lack of a tamper-proof audit trail also makes forensic investigations and incident response much more complicated.
Consequently, multiple technologies and solutions have been developed to address these risks, as well as provide better activity monitoring and threat detection. Covering all of them in just one product rating would be quite difficult. Furthermore, KuppingerCole has long stressed the importance of a strategic approach to information security.
Therefore, customers are encouraged to look at database and big data security products not as isolated point solutions, but as a part of an overall corporate security strategy based on a multi-layered architecture and unified by centralized management, governance, and analytics.
Ultimately, data security will not be solved until we somehow fully bridge the gap between protecting structured and unstructured data. As mentioned earlier, for customers, there is only “just data”, and the rest of the complexity should not be their concern. The same applies to “at rest” versus “in transit” versus “in use” - the distinction between these states is not as clear-cut anymore.
A working solution for this challenge would completely revolutionize the data security market. However, it has not happened yet and will probably not happen within the next few years.
1.1 Highlights
- Data Security Platform is a recently emerged term that better represents the customer demands for a universal data protection solution that “just works without getting in the way”, regardless of the data format, platform, or location.
- While vendors are also eagerly adopting the new name for their existing products, truly universal platforms that can bridge the divide between securing structured and unstructured data are yet to be seen.
- The whole data security market continues to transform. Some of the vendors covered in our previous Leadership Compass have been acquired, transitioned to private ownership, or rebranded and completely reinvented their entire portfolios. Even the large veteran vendors feel the pressure to evolve to meet the changing customer needs.
- A healthy mixture of traditional security vendors, companies that just entered the market, and innovative startups indicates that the market is still far from maturity, and everyone has an opportunity to gain recognition, especially among the innovation leaders.
- Even though this Leadership Compass recognizes several highly rated overall leaders, it is worth stressing that no single data security solution currently exists that can address every possible use case and customer requirement. Studying the capabilities of every vendor and product presented here is strongly recommended.
- The Overall Leaders in Data Security Platforms are (in alphabetical order) comforte AG, IBM, Imperva, Mage Data, Oracle, SecuPi, and Thales Group.
















































