1 Executive Summary
Traditional network security models have faced unprecedented challenges in adapting to the demands of a rapidly changing digital environment. As businesses embrace digital transformation and become increasingly cloud-native, mobile, and interconnected, the corporate network perimeter is gradually disappearing, exposing users to malware, ransomware, and other cyber threats. Traditional perimeter security tools no longer provide adequate protection from these threats. But even more so, traditional remote access solutions like virtual private networks (VPN) can no longer ensure the scalability and performance needed for the increasingly mobile and remote workforce.
VPN is a typical example of a technology that was never designed for the purposes it is used nowadays. Besides creating potential bottlenecks by forcing companies to backhaul remote users’ traffic to a central location and thus negatively affecting performance and productivity, VPN appliances grant those users full, uncontrolled access to entire local area networks (LANs). This dramatically expands the attack surface of corporate networks, provides easy lateral movement for potential attackers, and enables uncontrolled access to internal resources with implicit trust.
Unlike traditional perimeter-based security models that assume trust within the network, Zero Trust Network Access (ZTNA) adopts a more granular and identity-centric approach. An infrastructure designed around this model treats every user, application, or resource as untrusted and enforces strict security, access control, and comprehensive auditing to ensure visibility and accountability of all user activities. This Zero Trust philosophy has become increasingly relevant as organizations grapple with the proliferation of remote work, cloud adoption, and the growing sophistication of cyber threats. It is also important to emphasize that Zero Trust is not only about networks, but about identities, devices, systems, and applications. It is about ubiquitous and continuous verification of device security and identity authentication.
As a concept, ZTNA is based on the assumption that any network is always hostile, and thus, any IT system, application, or user is constantly exposed to potential external and internal threats. Often expressed as "never trust, always verify," ZTNA is an embodiment of the principle of least privilege, and at its core mandates that every access request be properly authenticated and authorized. Proper access management in service of ZTNA means considering the requesting user's attributes, authentication and environmental context, permissions and roles, source device information, and the requested resource attributes. Zero Trust Architecture implies a concept where clients can access services from everywhere, not relying only on internal network security mechanisms.
This approach ensures that access policies can be defined in a much more granular fashion per individual application or service by establishing secured point-to-point tunnels between clients and services. Each of these sessions is always authenticated and continuously monitored to prevent malicious activities. Access and security policies are managed centrally and enforced across hybrid IT environments (on-premises, multi-cloud, or mobile).
One of the fundamental misconceptions the industry experts are still struggling to explain to the public is that Zero Trust is not an off-the-shelf product, but a journey that begins with a long-term business strategy and focuses on a step-by-step implementation, using existing or readily available tools and technologies, while maintaining the continuity of business processes and avoiding adding even more complexity to the existing architecture. Overcoming these challenges requires a holistic approach, involving careful planning, stakeholder education, and collaboration with experienced cybersecurity professionals.
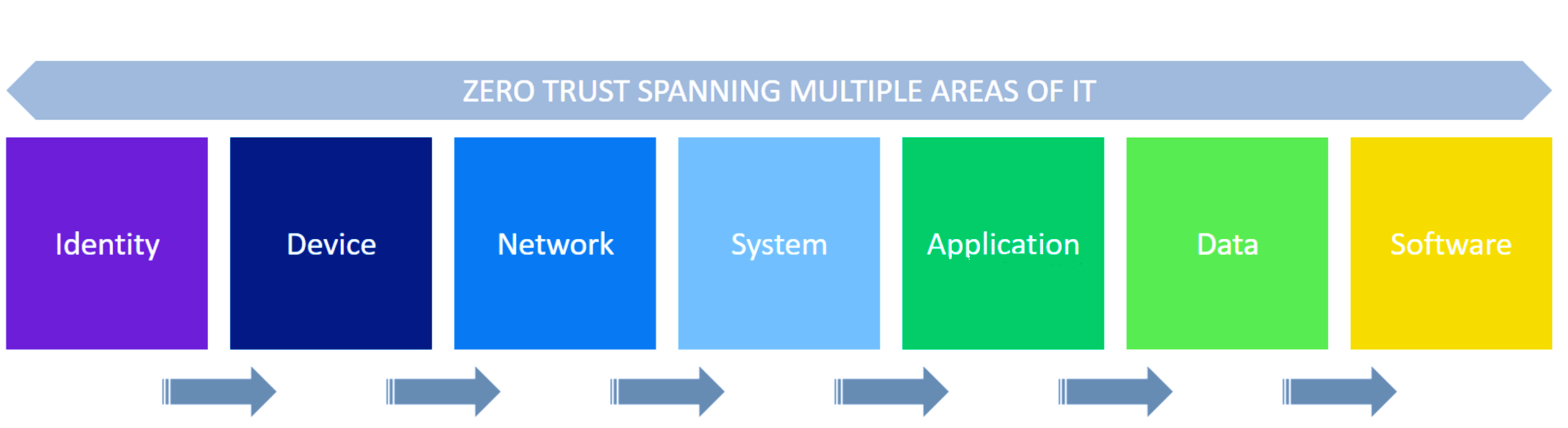
Figure 1: Zero Trust spanning multiple areas of IT
In this Leadership Compass, we provide an overview of the existing solutions implementing this approach. They might be based on different underlying technologies and focus on different aspects of the Zero Trust methodology, but fundamentally, all of them solve the same problem: enabling secure yet convenient access to business applications and other resources for users regardless of their location, whether in an office, at home or anywhere else. To better understand the fundamental principles this report is based on, please refer to KuppingerCole’s Research Methodology.
1.1 Highlights
- The market for ZTNA solutions is currently experiencing significant growth. Both large established vendors and small but innovative startups are offering a multitude of solutions that promise to address various usage scenarios: simplified cloud migration, seamless hybrid and multi-cloud architectures, or a modern replacement for VPN.
- KuppingerCole Analysts predicts that the Zero Trust Network Access Market will reach $7.34 billion in 2025, with a Compound Annual Grow Rate (CAGR) of 17.4%. The largest share of the global revenue in this market segment is North America, currently representing 47.4% of the total market size. It is followed by EMEA and APAC with 25.7% and 18.2% respectively.
- The emergence of the ZTNA paradigm signifies a pivotal shift in security strategy, reflecting the realization that the conventional castle-and-moat approach is no longer sufficient in safeguarding today's dynamic and distributed IT ecosystems. Unlike traditional perimeter-based strategies, ZTNA operates under the assumption that no entity, whether inside or outside the network, should be inherently trusted.
- Zero Trust architectures have gained enormous popularity as more secure, yet flexible and future-proof alternatives to traditional perimeter-based security. By eliminating the very notion of a trusted system, ZT architectures enforce strict identity verification and least-privilege access policies for every user, device, or application, regardless of where they are located.
- ZTNA is the key technology that enables modern Zero Trust architectures, together with comprehensive identity management, strong multi-factor authentication, and real-time behavior analytics. Besides dramatically reducing the attack surface and preventing lateral movement for hackers (and thus significantly improving security posture), it has the potential to greatly simplify both the users’ and administrators’ experiences.
- While ZTNA offers enhanced security by adopting a least-privilege access model, potential downsides include the need for careful implementation and potential complexity, especially in larger organizations.
- The Overall Leaders in Zero Trust Network Access are (in alphabetical order): Absolute Software, Akamai Technologies, Broadcom, Cato Networks, Check Point, Cisco, Cloudflare, Fortinet, Jamf, Lookout, NetFoundry, and Sophos.
















































