IoT, the Internet of Things, covers a wide range of technologies. My Fitbit e.g. is an IoT device, it connects to my smartphone which formats the data collected on my movements. Also, vehicles that communicate with diagnostic instruments and my home thermostat that I can control via the Internet are IoT gadgets.
This article, however, is concerned with a very particular type of IoT device: a sensor or actuator that is used in an industrial computer system (ICS). There are many changes occurring in the Industrial computer sector; the term Industry 4.0 has been coined as a term to describe this 4th generation disruption.
A typical ICS configuration looks like the following:
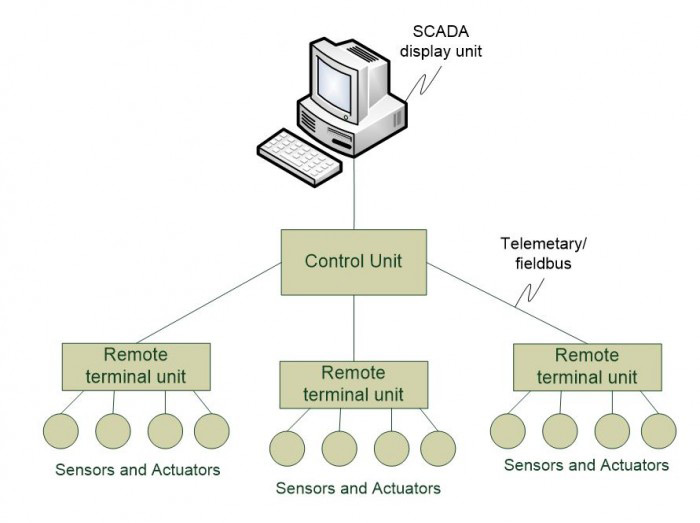
- The SCADA display unit shows the process under management in a graphic display. Operators can typically use the SCADA system to enter controls to modify the operation in real-time.
- The Control Unit is the main processing unit that attaches the remote terminal units to the SCADA system. The Control unit responds to the SCADA system commands.
The Remote Terminal Unit (RTU) is a device, such as a Programmable Logic Controller (PLC), that is used to connect one or more devices (monitors or actuators) to the control unit. It is typically positioned close to the process being managed or monitored but the RTUs may be hundreds of kilometres away from the SCADA system.
Communication links can be Ethernet for a production system, a WAN link over the Internet, a private radio link for a distributed operation or a telemetry link for equipment in a remote area without communications facilities.
So what are the main concerns regarding IoT in the ICS space? As can be seen from the above diagram there are two interfaces that need to be secured. The device to RTU and the fieldbus link between the RTO and the Control Unit.
The requirement on the device interface is for data integrity. In the past ICS vendors have relied upon proprietary unpublished interfaces i.e. security by obscurity. This is not sustainable because device suppliers are commoditising the sector and devices are increasingly becoming generic in nature. Fortunately, these devices are close to the RTU and in controlled areas in many ICS environments.
The interface to the Control Unit is typically more vulnerable. If this link is compromised the results can be catastrophic. The main requirement here is for confidentiality; the link should be encrypted if possible and this should be taken into account when selecting a communications protocol. Manufacturing applications will often use MQTT which supports encryption, electrical distribution systems will often use DNP3 which can support digital signatures, in other cases poor quality telemetry links must be used in which case a proprietary protocol may be the best option to avoid potential spoofing attacks.
One big benefit of the current developments in the ICS sector is the increasing support for security practices for operational technology. Whereas in the past there was a reliance in isolation of the ICS network, there is now an appreciation that security technology can protect sensitive systems while enjoying the benefits of accessibility. In fact, both worlds can be seen as siblings, focused on different parts of the enterprise. There already exist promising possibilities to enable this duality, e.g. this one. But understanding the technology is also important: One home automation equipment supplier released a line of sensor equipment with an embedded digital certificate with a one-year validity.
Conclusion: Despite all – yet partly unseen – benefits of connected things, there are still many pitfalls in vulnerable industrial networks and there is a massive danger of doing IoT basically wrong. The right path has still to be found and the search for the best solutions is a constant discovery process. As always, one of the best ways to success is sharing one’s experiences and knowledge with others, who are on the same journey.
















































