Proactive Cyber Security needs TDIR
Organizations and society in general have become more and more dependent on IT delivered services. This has increased the potential impact of risks from cyber-attacks. Cybersecurity needs to meet this challenge by moving beyond the traditional approach of protection, detection, and response.
Limit Attacker Free Time
The old model of a risk arising from a largely static threat exploiting a known vulnerability to cause damage is no longer adequate for today’s cyber environment. The cyber “Kill Chain” explains how threat actors are active within the cyber infrastructure well before a vulnerability is exploited. Therefore, it is not sufficient simply to remove known vulnerabilities - it is essential to detect cyber threat activity prior to the attack to actively prevent this from succeeding.
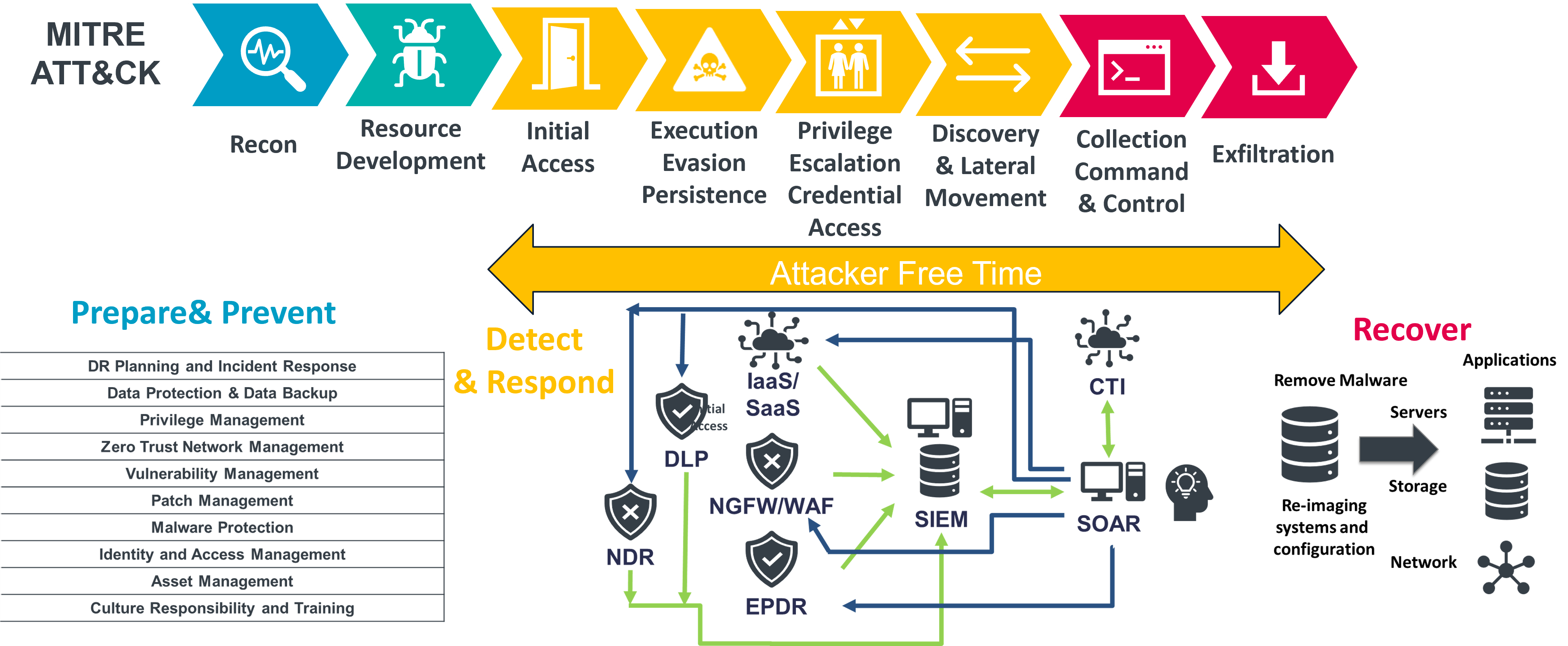
Figure 1: TDIR to Limit Attacker Free Time
The level of risk from cyber-attacks such as ransomware is now so high that it is a question of when not if a cyber-attack on your organization’s business critical cyber infrastructure will succeed. However, while most organizations have invested heavily in cyber prevention, surveys reveal that they are less well prepared to recover from a cyber-attack.
Authorities around the world have recognized these challenges and are imposing stricter requirements on organizations that their populations rely on for a wide range of essential services, which includes a wide and growing number of private companies that should be preparing now to meet their new obligations.
Notably the EU issued the Network and Information Systems (NIS) Directive in 2016 and the US saw the introduction of Executive Order 14028 on Improving the Nation's Cybersecurity in 2021. But European authorities are now seeking to go even further with an update to the NIS Directive, known as NIS2, which is expected to go into force by the second half of 2024.
Unlike its predecessor, NIS2 has a much wider scope, going beyond the traditional critical national infrastructure providers to include a range of organizations that are essential for the normal functioning of society, which include both EU and non-EU organizations that will have to ensure their compliance in future.
Threat Detection and Incident Response
All these factors taken together have led to a growing market in Threat detection and Incident Response tools and services.
Threat intelligence – the threat actors reuse and repurpose the techniques, tools, and processes (TTPs) that they use. This makes it vital that where these are identified, this information can be securely shared amongst potential victim organizations. This information Information about threats, TTPs, and devices that adversaries employ; the systems and information that they target; and any other threat-related information that provides greater situational awareness.
Organizations should join the cyber threat intelligence networks relevant to their industry and location. They should also make sure that their cyber-security teams or service providers receive and share cyber threat intelligence from trusted suppliers.
Threat Detection – there is a wide range of tools that are intended to help to detect abnormal activity within and around the organizational systems. These include Security Event Information Monitoring (SIEM), Security Orchestration, Automation, and Response (SOAR), Endpoint Protection Detection & Response (EPDR), Network Detection and Response (NDR), and Extended Detection and Response (XDR). In general, these tools ingest the vast amount of data logged by the various sensors around the IT infrastructure and provide capabilities to filter and analyze this data to detect anomalies. The challenges are the sheer volume of data and avoiding false positive overload.
Organizations should implement or outsource these activities in a way that is integrated with relevant threat intelligence. Look for the application of Machine Learning (ML) / Artificial Intelligence (AI) based approaches to improve the detection of actual threats. Look for integration with attack path analysis and to help to prioritize the actions needed on threats detected.
Attack Surface Management – business applications and the cyber infrastructure upon which they depend will contain vulnerabilities or weaknesses that could be exploited by cyber adversaries. Many of these will already be known and documented as Common Vulnerabilities and Exposures (CVEs) for which there are patches or workarounds to remove them. Attack Surface Management tools help organizations to find these vulnerabilities and together with attack path analysis tools to prioritize and close them.
Organizations should implement a continuous vulnerability detection and assessment process to remove known vulnerabilities. They should subscribe to and act on feeds providing newly discovered vulnerabilities.
Data Resilience – data is the most important asset of the modern organization, and it needs to be protected against ransomware as well as loss. Cyber adversaries use various techniques to infiltrate an organization’s IT systems and make changes that prevent the organization from accessing their data and using their IT services. Cloud services create challenges and cloud infrastructure is data defined. Organizations can misunderstand the shared responsibility model and believe data protection is the sole responsibility of the cloud provider. In addition, Big Data and massive data lakes held in cloud services create additional data resilience challenges.
Backup and Disaster Recovery tools provide important controls that are needed to recover data and restore services following cyber-attacks. Organizations need to implement and regularly these tools as part of their Business Continuity processes.
Incident Response - Organizations need a plan for managing incidents and this must be prepared and tested in advance of an incident occurring. When a major incident is suspected there must be a clear process for invoking a major incident response. The key elements of this are having an incident response team who know what their roles are and that can be assembled when needed. A command structure with a clear chain of command and definition of responsibilities. A communications plan to manage communications with all those involved when and incident occurs. Recovery and restoration – the process for removing the vulnerabilities, restoring the affected systems and data, and then safely resuming their normal operation. Notification – the process for meeting your organization’s statutory obligations for notifying regulators and customers about the incident.
Organizations should retest this plan at regular intervals.
Dynamic Cyber Security
Cybersecurity spending will never be able to grow as fast as attacks increase. Just trying to defend is not sufficient – organizations must get ahead of the cybercriminals and move beyond current approaches to cybersecurity by understanding the external threat landscape. Cybersecurity needs to keep up with this rapid pace of change by taking their focus beyond the traditional approach of protection, detection, and response, to become proactive.
















































