Why you should Regularly Review your Cyber Security
Cyber security is never done – you need to constantly work to improve your organization’s cyber security readiness. Cyber adversaries never sleep and the geopolitical tensions across the world are raising the cyber security threat levels.
Technology is evolving
The technology landscape is evolving creating new opportunities as well as new threats. Lange Language Models (LLMs) have evolved beyond what was thought practical only a few years ago and conversational Artificial Intelligence engines are now a commodity.
Organizations are adopting these to provide improved efficiency and effectiveness of their operations and a better connection with their customers, partners, and suppliers. However, while LLMs provide great opportunities, they also bring new cyber threats.
AI involves a new kind of development pipeline and current system development methodologies and tools are not yet adapted to this. Can you be sure of the provenance of your training data? Can you trust the shared LLM? Can you be sure that the deployed inference engine has not been poisoned?
LLMs represent an entirely new form of cloud workload. Current Cloud Native Application Platforms (CNAPP) and Cloud Security Posture Management (CSPM) do not cover these.
However, LLMs provide powerful capabilities to enhance the identification of cyber risks, the detection of active threats and the response to and recovery from cyber-attacks.
Organizations cannot afford to neglect the new opportunities but must prepare for these new threats. They must also exploit these new capabilities to improve their cyber security.
Standards and Regulations are Developing
The standards and best practice frameworks for cyber security are changing to respond to the increasing level of cyber threats and to incorporate the latest industry insights into how to best respond to these.
ISO/IEC 27001 The widely used information security standard ISO/IEC 27001 was updated in 2022. This new standard includes completely new controls covering - Threat intelligence, Information security for use of Cloud services, ICT readiness for business continuity, Physical security monitoring, Configuration management, Information deletion, Data masking, Data leakage prevention, Monitoring activities, Web filtering and Secure coding.
If your organization complies with ISO 27001 you will be required to update your controls to meet the new standard when next certified. Are your IT service providers and cloud services certified to the new standard?
NIST Cybersecurity Framework (CSF) v2.0 - On August 8, 2023, NIST released a draft of the NIST CSF 2.0, making the most significant revision to the framework since its inception in 2014. The draft includes the CSF itself and a discussion draft of implementation examples. NIST intends to release the final version in early 2024 without issuing another version for public comments.
NIST’s CSF 2.0 version 2.0 introduces significant changes to the cybersecurity landscape to address evolving threats and make the framework more accessible to all types of organizations. The draft reflects community feedback and industry shifts, emphasizes the role of cybersecurity as a key enterprise risk, and expands its scope beyond critical infrastructure. The CSF now includes six core functions: identify, protect, detect, respond, recover and the new “govern” function, which focuses on decision making in support of a cybersecurity strategy.
If your organization bases its approach to cyber security on this framework you need to plan for transition to the updated version. Are you ready for this transition?
EU NIS 2 - In the wake of increased cyber-attacks on national critical infrastructure, authorities around the world are imposing stricter requirements on organizations that their populations rely on for a wide range of essential services, which includes a wide and growing number of private companies that should be preparing now to meet their new obligations.
Notably the EU issued the Network and Information Systems (NIS) Directive in 2016 and the US saw the introduction of Executive Order 14028 on Improving the Nation's Cybersecurity in 2021. But European authorities are now seeking to go even further with an update to the NIS Directive, known as NIS2, which is expected to go into force by the second half of 2024.
Unlike its predecessor, NIS2 has a much wider scope, going beyond the traditional critical national infrastructure providers to include a range of organizations that are essential for the normal functioning of society, which include both EU and non-EU organizations that will have to ensure their compliance in future.
Is your organization ready to comply with its obligations under these new regulations.
Reviewing your cyber security
Business objectives, organizational best practices, and technologies are constantly evolving. It is essential to continuously review your organization’s performance in the light of these changes. To support these reviews, KuppingerCole provides Maturity Level Matrices that are specifically targeted to distinct areas of cyber security.
These are based on the five-point maturity scale formulated using the Carnegie Mellon Maturity Index (CMMI). Note that this is currently being enhanced to include best practices for measuring capability and improving performance in the areas of people management, data management, and virtual work.
Assessing maturity based on this model is complex and to organizations to accomplish this task for cyber security we publish two matrixes that describe the key areas that must be considered when assessing cyber security maturity. There are two matrices one covering cyber security organizational and management maturity and the other technological maturity. These are summarized below.
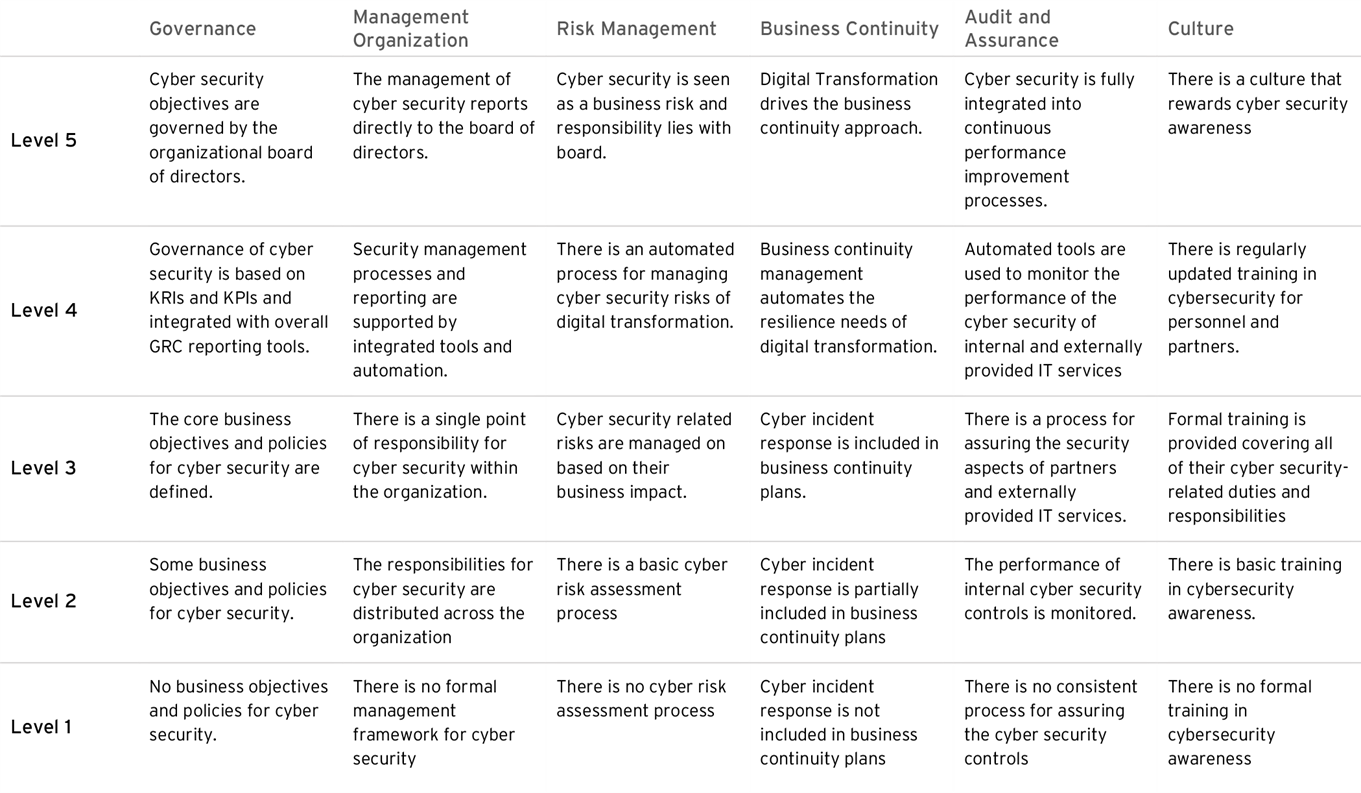
Figure 1: Cyber security organizational and management maturity
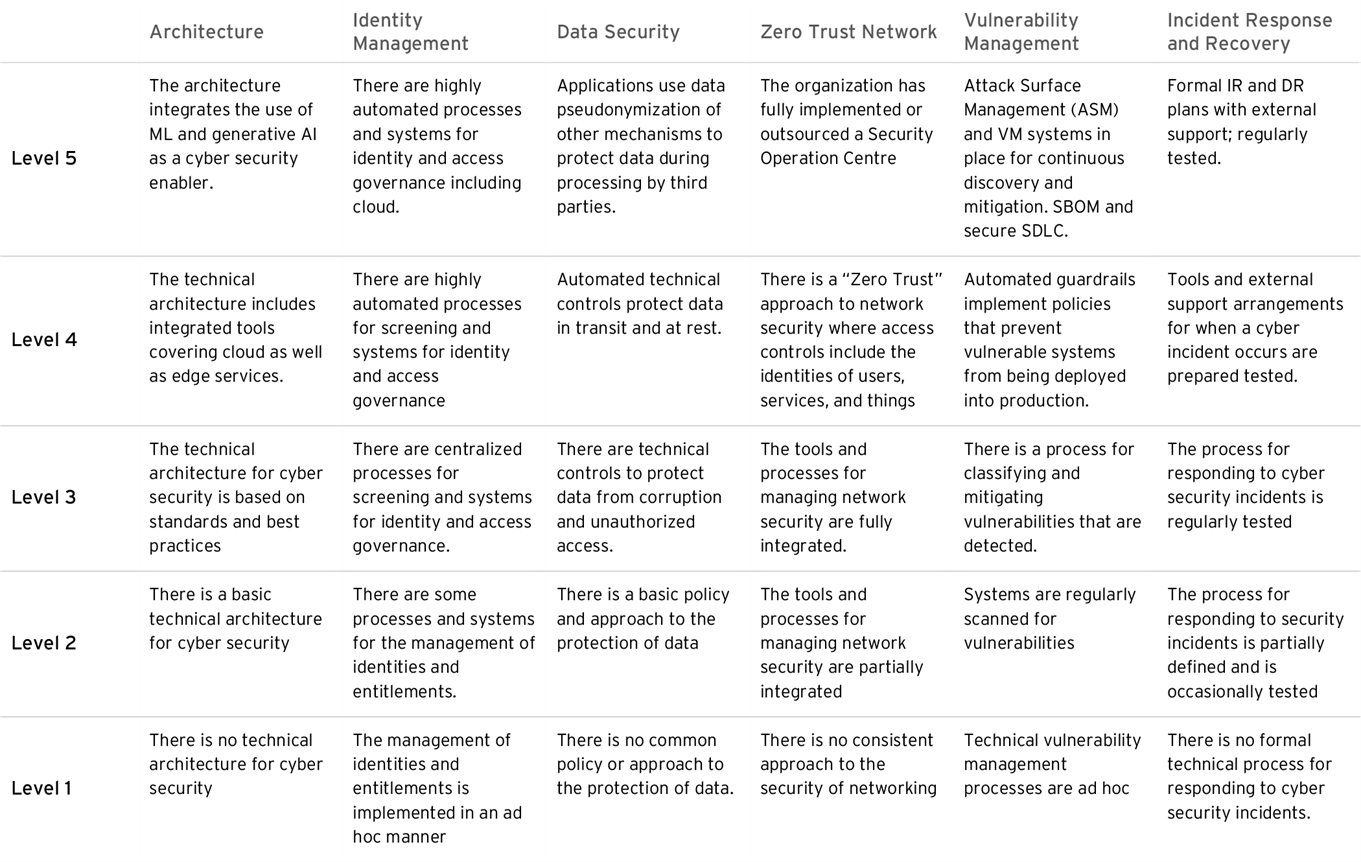
Figure 2: Cyber Security Technological maturity levels
KuppingerCole provides deep research into all the areas of cyber security. There also are many useful sessions from our cyberevolution event including how the hackers can exploit AI, the regulatory challenges to the financial industry from DORA, as well as practical advice on cloud security.
We invite you to also attend our flagship conference EIC in Berlin June 4th to 7th, 2024.
















































