5G Identity and Authentication
5G is the next generation of cellular mobile communications intended to support the massive increase in capacity and connectivity that will be required for the future cloud of things and to provide the enhanced bandwidth needed for new mobile data services. The security of both depend upon being to identify not only the people but also the things that are using the network services. Organizations need to act now to take account of how 5G will impact on their identity and access management governance and processes.
5G identifiers
First it is important to understand how identity is handled by public cellular networks. This is because many “things”, including cars delivery vehicles and others, will use 5G and identify themselves in this way to access the network. The original objective for this identification was for the network provider to ensure that only the authorized customers have access to the service and that this use cannot be repudiated. How this is achieved has evolved over time to meet the increasing challenges of fraud and cybercrime.
There are 2 primary identifiers for a cellular device. The first is the IMEI (International Mobile Equipment Identifier) – this identifies the phone and is used to block access by stolen devices. Within the device is a SIM (Subscriber Identity Module) – which is a trusted tamper resistant hardware module. The SIM contains two key pieces of data – the IMSI (International Mobile Subscriber Identity) which is sometimes known as the SUPI (Subscriber Public Identity) and a shared key Ki. This key is used in the AKA (Authentication and Key Agreement) protocol when the device connects to the cellular network.
5G Authentication
The device would normally connect to the Home Network (i.e. the network with which the user has a contract) and be authenticated directly. However, when the user is roaming the device could connect via a Serving Network. One of the weaknesses of 4G and earlier was the involvement of the Serving Network in the authentication process and one of the key changes at 5G is that the authentication decision is always made by the Home Network.
The authentication process starts with the device requesting access by sending its IMSI / SUPI to the network. Previously this was sent unencrypted, posing a threat that it could be intercepted and reused, in 5G this is always encrypted using the public key of the Home Network. The Home Network responds to this request by sending a Authentication Vector (a large random number) to the device. The device must encrypt this using the shared key Ki and send this as the response. Since the Home Network has a copy of the key it can check that the decrypted response corresponds to the value that was originally sent. Prior to 5G this check could be made by the Visited Network that held a copy of the expected response. 5G and 4G also provide mutual authentication allowing the device to authenticate the network using the AUTH (Authentication Token) returned by the network and the shared key.
Once the device has been authenticated in 5G the protocol goes on to agree how the traffic will be encrypted and subsequent messages use a SUCI (Subscriber Concealed Identity) to identify the device. In 5G traffic is encrypted throughout the infrastructure whereas in earlier generations it was only encrypted over the radio link.
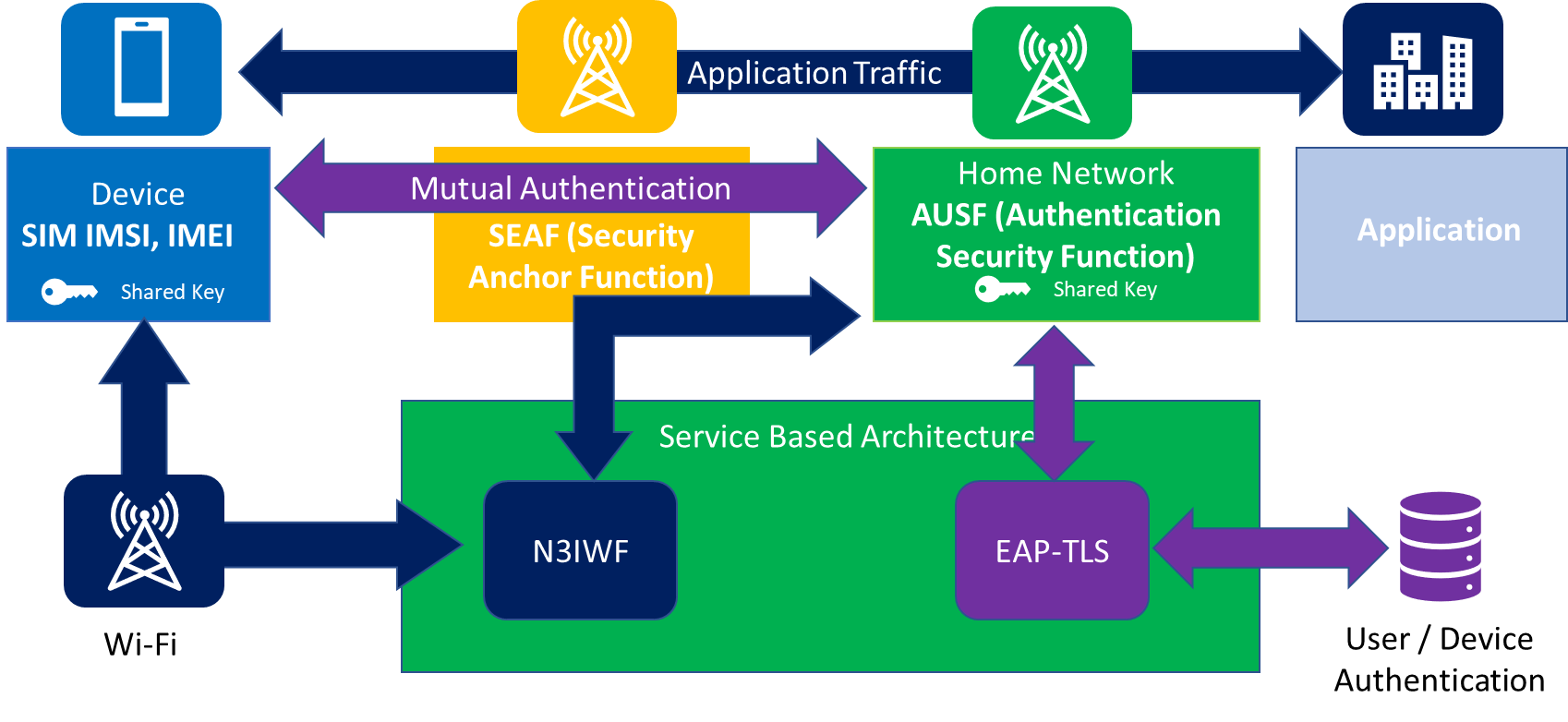
Figure 1: 5G SIM based Authentication Overview
5G Extensible Authentication Protocol
However, not all devices under all circumstances may want to use the 5G-AKA protocol. For example, in a private 5G network a large manufacturing plant may wish to use a central directory of devices to control access. To enable this the 5G architecture provides a unified authentication framework that makes 5G authentication both open and network agnostic. It supports access through other kinds of network including Wi-Fi and cable via the N3IWF (Non-3GPP Interworking Function).
For specific use cases such as IoT and private 5G networks EAP-TLS (Extensible Authentication Protocol Transport Layer Security) is also supported. These other forms of authentication could be useful for very cheap IoT devices, for example small sensors, for which it would be prohibitively expensive to require SIM cards. In addition, the 5G system can be deployed as a replacement for Wi-Fi in an enterprise or factory setting and this can reuse the existing public key and certificate infrastructure for network access authentication.
When selected as the authentication method EAP-TLS is performed between the device and the AUSF through the SEAF which transparently forwards EAP-TLS messages back and forth between the device and the AUSF. For mutual authentication, both the device and the AUSF can verify each other’s certificate. This makes it possible for the AUSF to implement any of the common enterprise authentication protocols including RADIUS, Kerberos or others.
| 4G | 5G AKA | 5G EAP TLS | |
| Identity | SIM | SIM | Other |
| Trust Model | Shared Symmetric Key | Shared Symmetric Key | Public Key Certificate |
Recommendations
5G will impact on many industry sectors including logistics, manufacturing, transport, healthcare, the media, smart buildings as well as local government. Managing who and which devices can access what applications and services is critical to ensure security and safety. Managing vast access by the potentially enormous number of devices adds to the significant existing identity and access challenges. Organizations should act now to:
- Integrate your IoT security architecture with existing IAM and Access Governance frameworks.
- Define authentication and access controls for IoT devices based on the levels of threats to your use cases.
- Use strong authentication for sensitive devices (consider SIM / embedded SIM or certificates).
- Take care to secure and remove vulnerabilities from IoT devices – especially change default passwords.
- Integrate IoT device management with other IT asset management systems
- Review how your existing PKI processes will be able to support the number if IoT devices.
For more details on this subject see KuppingerCole Leadership Brief 5G Impact on Organizations and Security 80238. Also attend the Public & On-Premise Cloud, Core IT Hosting, Edge IoT Track at EIC in Munich on May 13th, 2020.
















































