During my Opening Keynote at this year’s EIC (European Identity & Cloud Conference, www.id-conf.com), when talking about the Top Trends in IAM, Mobile Security, GRC, and Cloud Computing I used the term “Identity Explosion” to describe the trend that organizations will continue (or start) to re-define their IAM infrastructures in order to make them future-proof. I talked more about that in my presentation on “Re-engineering IAM to better serve your business’ needs” later during the conference. Interestingly, I heard the term “Identity Explosion” being used several times in other sessions after that, referring to my keynote.
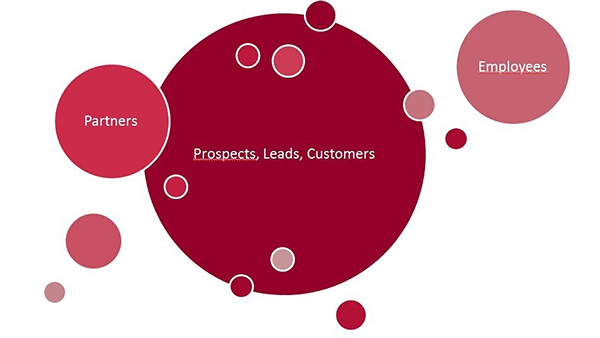
So today I want to look at that buzzword, at what’s behind the buzzword, and the impact of this “Identity Explosion”. When looking at IAM (Identity and Access Management), it’s about managing users and their access. However, most of the IAM infrastructures in place today were mainly built with the employee in mind. Even today I frequently observe in advisories that projects begin by starting with a focus on some (relatively) small groups of users, like the employees, some temporary workers, or maybe some of the business partners. However, the reality of many organizations is that they have – to use a real-world number – perhaps 28,000 employees and 4.5 million customers to deal with.
Thus one of the initial discussions in such advisories is always about ensuring that the scope is set wide enough: It is about looking at all potential types of users, at least during the conceptual phase. Organizations might start implementing for the internals, followed by business partners, and then the customers (and leads and prospects and suspects). But the design has to have the “Identity Explosion” in mind: This massive growth in the number of of identities to deal with. That starts with simple things like the structure of identifiers and ends with scalability issues and the integration of different technical approaches, for example versatile, risk- and context-aware authentication and authorization. I’ve seen companies struggling with the identifiers they have chosen only with employees in mind spending a lot of money to fix that.
But it is not only – and not even mainly – about the costs. It is about agility. If IT is not prepared to deal with all types of users and provide identity and security services for them, then IT will fail in supporting the business demands. These are about integration with partners and a tight interaction with the customers (and leads and so on). IT has to be prepared for that. It has to understand that there will be this “Identity Explosion” anyway, with a massively growing number of identities to deal with.
An interesting aspect which isn’t yet discussed much in this context is business policies, including segregation of duties. How do you deal with the situation in which the same person (e.g. you or me) could have at the same point in time the identity of a customer, freelance broker, and employee of the same insurance company? Three identities which have to be understood and managed: The same person might sell an insurance contract to himself and approve it, using three different identities.
And what I’ve discussed so far is just a small bang. The big bang is about the “Internet of Things”, at least for many organizations. An automotive vendor has to deal not only with his customers, dealers, employees, and suppliers. He also has to deal with the cars themselves, which again split up into many devices with their own “identity”. This again will increase the number of identities to deal with.
Having the “Identity Explosion” in mind when working on strategies, concepts, and implementation of IAM and all the related technologies helps avoid solutions which can’t scale with the changing business requirements. Thus looking at your current IAM and thinking about how to get ready for that is one of the things you should start doing now.