It looks like the whole world is currently talking (at least, tweeting) about the latest large-scale Twitter hack. High profile accounts of the likes of Barack Obama, Joe Biden, Bill Gates, and Jeff Bezos, as well as companies like Apple or Uber, were suddenly promoting a cryptocurrency scam. At first, they referred to a specific crypto-related website, but as it was quickly taken down, the hackers switched to spreading multiple Bitcoin addresses, asking people to send money to them to get a double amount of their investment back.
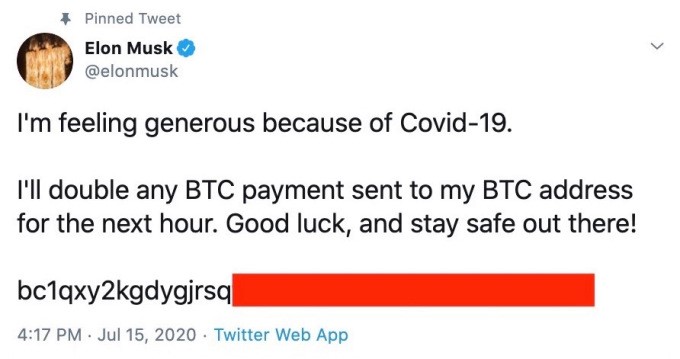
Even though this type of scam is nothing new and should look obviously suspicious to anyone, the sheer size of the Twitter platform allowed hackers to reach enough gullible people to collect over $100,000 within hours.
The hack was an inside job
Looking at the number of accounts affected (including major corporations with strong security practices), it quickly became obvious that the attack was performed by a single actor with a possibility of it being an insider job at Twitter. The company later confirmed “a coordinated social engineering attack by people who successfully targeted some of our employees with access to internal systems and tools.”
Several screenshots of the alleged internal tool have also leaked, showing what an employee could do to an account, including changing the email address linked to it to prevent legitimate owners from restoring their access. Various press outlets are currently speculating about the methods the hacker could have gained access to this tool from a Twitter employee: was it really a social engineering attack or an action of a malicious insider.
Inconvenient assumptions
For me, however, this is by far not the biggest question. Judging by the attack timeline and Twitter’s reaction to it, it becomes rather clear that they were not aware of malicious activities happening on such a massive scale until the attack was already underway, causing public outcries and even calls from concerned politicians. Does it imply that the company has no appropriate security monitoring tools in place, which would have at least alerted about suspicious behavioral anomalies in their network?
Also, the idea of employees having unchecked access to such powerful administration tools, giving them a potential ability to manipulate any account, access sensitive personal data, or even post on their behalf raises a lot of concerns. Does Twitter even have any privileged access controls in place for these tools? How could it be compliant with regulations like GDPR and CCPA?
What can users do?
Can we even trust anything posted on the platform anymore, if nobody can be protected from such attacks, not even Elon Musk or Donald Trump? And by the way, who is supposed to be held responsible for this debacle? The first thing I tried to do after I’ve read about the attack is to find the name of Twitter’s chief security officer. But apparently, the company does not have one since 2018…
Finally, what can we the users do? Nothing apparently. Protecting sensitive systems from malicious insiders can only be done, well, from inside the company. Unfortunately, it’s apparently too late to teach Twitter about PAM, compliance and security best practices, but at least we could teach you… Check out our latest KCLive Event on Privileged Access Management, for example – this could be a good start towards becoming smarter than Twitter!
















































