Playlist
Advanced Privileged Access Management & New Trends
Show more
10 videos in this playlist
Event Recording
Paul Fisher: In the Future PAM will Become Embedded in the IT Stack
Aug 21, 2020
Paul Fisher will expand on his analysis of how Privileged Access Management platforms will develop support for DevOps and other key users. This will mean that certain PAM functions will be embedded within the technology stack, opening up password free and secure access paths and enable rapid task fulfilment.
Event Recording
John Ovali: Privileged Access Management – Motivation and Benefits
Aug 21, 2020
Why PAM is a must and how you can benefit from it: Many corporations need to comply with regulations which result in extended logging and monitoring of privileged activities. The Presentation shows how to start a successful PAM implementation and how to benefit from it.
Event Recording
David Wishart: How to Solve the Top 5 Access Management Challenges in Hybrid Cloud Environments
Aug 21, 2020
SSH.COM polled 625 IT and application development professionals across the United States, United Kingdom, France, and Germany to find out more about their working practices. We found that cloud and hybrid access solutions, including privileged access management software, slow down daily work for IT and application development professionals. These hurdles encourage users to take risky shortcuts and workarounds that put corporate IT data at risk.
Join SSH.COM’s David Wishart, VP Global Partnerships, to learn:
Why the user experience of the...
Event Recording
Jens Bertel Nykjær: Implementing PAM, How Did We Get Support and Buy-In From the Organisation?
Aug 21, 2020

Event Recording
Joseph Carson: Privileged Access Cloud Security: Insider Tips and Best Practices
Aug 21, 2020
As the adoption of cloud applications and services accelerates, organizations across the globe must understand and manage the challenges posed by privileged access from remote employees, third parties, and contractors. With 77% of cloud breaches due to compromised credentials, making sure your users get easy and secure access to the cloud should be a top priority. Join Thycotic chief security scientist and author Joseph Carson as he explains a practical approach to help you define and implement privileged access cloud security best practices. He will also share how Thycotic’s...
Event Recording
Vibhuti Sinha: Cloud PAM on the Rise: The Future is Now
Aug 21, 2020
The new normal demands organizations to enable remote workplace in a rapid and secure way.
The new normal requires privileged asset owners to make intelligent, informed and right decisions even with a fragmented view of risk.
The new normal requires governance to be integrated and inherent with privileged access workflows and not an after-thought.
This session would give insights and best practices to create the least privileged model, minimizing the risks associated with standing privileges and prepare enterprises to rapidly transform...
Event Recording
Rohit Nambiar: Cloud PAM: Challenges, Considerations And Approach
Aug 21, 2020
As Enterprises transitions to IaaS, Cloud Security and specifically IAM strategy and execution becomes crucial. IAM controls for IaaS/Public Cloud need to identify, secure and monitor Privilege Assets at the same time deal with the inherent elasticity, scalability and agility of the Public Cloud . As such a Privileged Access Management Program for Cloud i.e Cloud PAM is required to meet the increasingly stringent compliance and audit regulations and keep enterprises secure.
Event Recording
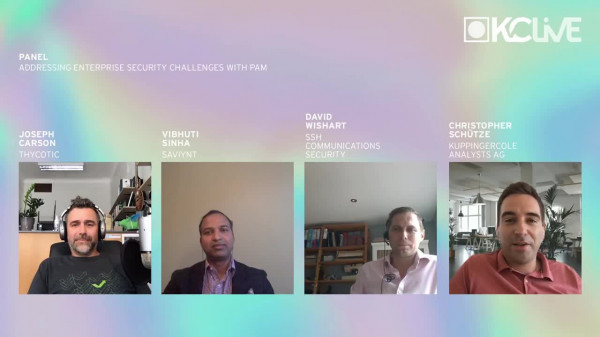
Panel - Addressing Enterprise Security Challenges with PAM
Aug 21, 2020

Event Recording
Alexander Koerner: Success Factors PAM Projects
Aug 21, 2020
Often I saw in the planning of PAM Projects that the Manager „only“ plan the implementation of the tool. It was a quite good installation but the project was not successful. Here some points I learned to have the customer happy and bring the Project to success:
Right Projectplanning with the right scope
The Right Strategy
Hand Over to run phase
Documentation
Interfaces to other Systems
Lessions Learned