1 Introduction
The landscape of enterprise and personal computing technology is continuously evolving. It didn’t seem that long ago, where the work environment consisted of a desktop computer and a landline phone. Traditional management of the desktop computers relied on manual updates of software and patches that were layered on top of each other. Later, “Gold Images” of desktop operating systems were used to provide a good know state of the OS but still required patches on a routine schedule, which would become what was known as traditional management.
As mobile phones became economically available, laptops and tablets computers replaced many stationary desktop computers; the business could control the employee device regarding it’s OS and software applications used as well as security controls when the device was within the perimeter of the organization. Client management tools were used to manage these environments. Client management involves capabilities such as OS deployment, software distribution, patch management, monitoring, and remote-control tools to support administration or to help automate other support functions that are typically executed manually.
Later, organizations needed to quickly deal with the introduction of the bring-your-own-device (BYOD) paradigm shift. Organizations required policies to define the boundaries of BYOD that included the ability to segregate the business data and applications from personal data and applications. Mobile device management (MDM) provided the tools to control the device functionality and help manage the lifecycle of these mobile devices and their platforms. Enterprise Mobility Management (EMM) solutions added mobile information as well as application and content management. The ability to push software, updates or patches to devices become what is known as modern endpoint management.
Since then, work environments are continuing to change. The range of endpoint device types have expanded past desktop, laptop, tablets, and mobile phone to now include printers, IoT devices, wearables like Apple Watch, and even newer types of endpoint devices that support virtual/augmented/mixed reality environments using headsets such as Oculus and HoloLens. Businesses are seeking to improve productivity and efficiency, while employees want to work from anywhere at any time. And with the more recent Covid-19 world we live in today, the requirement to work from home has become imperative, which requires the use of mobile devices to access enterprise applications and data as if they were in the office.
Given the complexity and growing number of different types of technologies involved in linking employees to corporate data both on-premise and in the cloud, mobile device management has gone through several iterations and approaches, with many enterprises now standardizing on a Unified Endpoint Management (UEM) approach.
This KuppingerCole Leadership Compass provides an overview of vendors and their product or service offerings in a certain market segment. This Leadership Compass focuses on Unified Endpoint Management from vendors from more localized geographic region to vendors with a global presence. It considers these services in the context of the hybrid, on-premises, and cloud, with IT services delivery models commonly now found in enterprises.
1.1 Market Segment
Endpoint Management is a market category that runs under a variety of names, such as Client Lifecycle Management, Unified Endpoint Management, and others. However, we see a clear trend towards comprehensive solutions supporting a variety of capabilities and types of endpoints. Thus, this Leadership Compass focuses on what is commonly referred to as Unified Endpoint Management. In this context, endpoints can be defined as traditional desktop or laptop computers, smartphones, tablets, wearables, printers, Internet of Things (IoT) devices, and even Virtual Reality (VR) headsets.
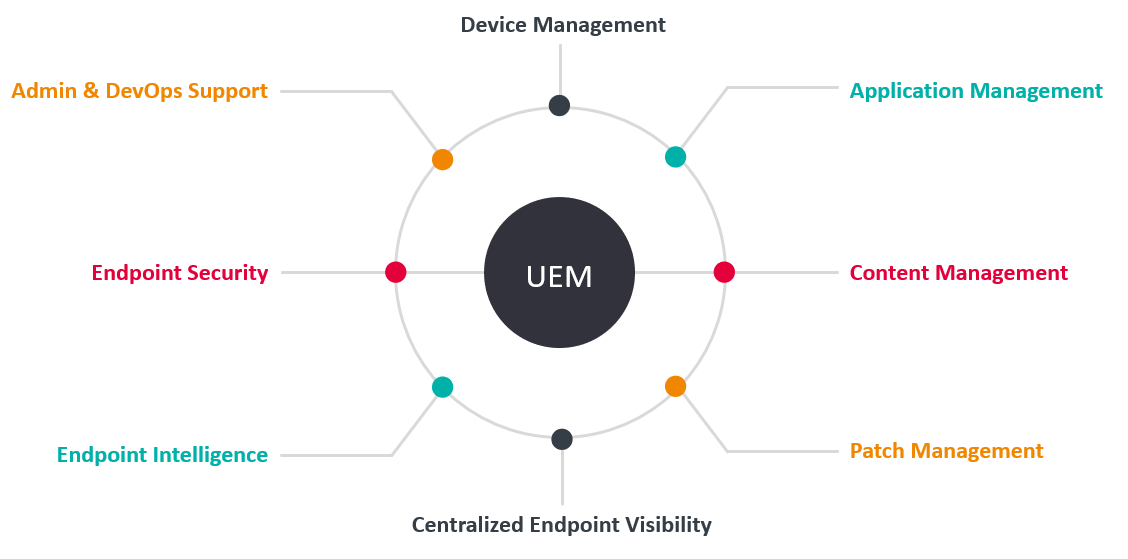
What is sometimes called client or service management involves capabilities such as OS deployment, software distribution, patch management, monitoring, and remote-control tools to support administration or to help automate other support functions that are typically executed manually. This type of management is also used to manage endpoint lifecycle, such as with UEM application management. Client management is a market segment in transition. Unified Endpoint Management (UEM) and Workspace Management are two of the major trends in client management.
A trend that has already become apparent in recent years has now become established. The separation between classic client management, which is usually based on Windows, and the management of mobile end devices (EMM, Enterprise Mobility Management) is now the exception rather than the rule. Most of the leading providers are focusing on Unified Endpoint Management, i.e., on solutions with which all types of end devices can be managed, from the variety of different desktops operating systems such as Windows, macOS, Linux or Chrome to mobile end devices with Android or iOS as the operating system.
The range of functions offered by such solutions now goes far beyond classic client management. It also includes the provision of configured work environments for employees, inventory, management of the operating system and applications, including security management, but also the management of content on end devices, for example, with the separation of personal and business apps and data.
Patch management, which a few years ago was often a separate product category, is also typically part of UEM solutions to the extent required today. Specialized solutions are still available, and patch management is also available in endpoint security solutions. However, most UEM products today also provide patch management functionality. Endpoint security can also be included in UEM, which sometimes intersects with other Endpoint Detection & Response (EDR) products. More information on this topic can be found in the KuppingerCole Buyer's Compass: Endpoint Detection & Response (EDR).
In addition to these influencing factors of workspace and user device expectations, other factors need to be considered when deciding how client management will be designed in the future. These include changes in application provisioning, client management from the cloud, integration with ITSM (IT Service Management) solutions, and the different concepts for client management on the one hand and for the provision of virtual work environments, i.e., the Digital Workspaces, on the other.
Here are some considerations of UEM solutions that this Leadership Compass covers:
- Products that are more classic software solutions that are installed and operated locally
- Cloud and hybrid UEM solutions
- Providers that have options for operation "as a service" that allow complete UEM to be obtained as a service without the need to install and operate servers locally
- The areas of UEM that the solution focuses on (e.g. device, application, security, patching, etc.)
- The breadth of operating systems and device types that the solution can support
- The depth of endpoint life cycle management the solution provides
- The level of application software, packaging or patch management
- Solutions that provide endpoint content management and containment capabilities
- The strength of the solutions endpoint security.
Ultimately, the selection of any UEM solution on the market will depend on the organization’s particular requirements, which may depend on many other aspects such as existing infrastructure management or other IT solutions currently being used today. For example, if a specialized endpoint security solution is already in use, this functional area of UEM solutions is less or not at all relevant. Or if the organization only needs to focus on device and patch management capabilities, then maybe some fully-featured UEM solutions may not be required, and a UEM solution with those specific features may be a better fit. In all cases, it is recommended that a structured selection process should be carried out before the product decision is made.











































